Spam and phishing attacks may originate from a dark web marketplace, but a user has to download something infected from that marketplace to release malware. Another problem with this system is that there’s increasing evidence that law enforcement agencies — such as the FBI — run and operate large number of exit nodes. This means that if you do anything illegal on the dark web and are unlucky enough to be routed through one of these nodes, the authorities will be well aware of what you’re doing. The dark web refers to the subsection of the deep web that provides illegal services.
Mullvad VPN

In fact, create new throwaway accounts and documents if possible. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. Avoid using payment methods that can easily expose your identity. Today, many organizations exist that are created only to handle these reports anonymously and effectively.
ZeroBin is a wonderful way to share the content you get from dark web resources. It is a reliable messaging tool where you copy/paste a text or image and send it to your addressee. Cryptocurrencies such as Bitcoin have been the dark web currency even before they became available to the general public.
“Resucitando” A La Tortuga De Floreana
However, this feature is only available on iOS, Android, and Windows. A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online.
What Is The Deep Web And How Do You Access It?
However, the technology that Yippy manages, was created in Carnegie Mellon. In addition, this included the acquisition of an unlimited license for the software known as Vivisimo’s Velocity, acquired by IBM in 2012 and renamed IBM Watson Explorer. However, you’ll have to be mindful of this resource as it includes both legal and illegal destinations. And there might be legal and ethical implications involved when navigating this site.
Other Ways To Access Dark Web Platforms
TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki. It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it.
How To Access The Dark Web
He also leads the video production team and helps craft e-courses on online technology topics. Outside of the professional realm, he is a digital nomad with a passion for traveling, having lived in many countries across four continents. This VPN has various features that keep you safe on and off the dark web. It uses 256-bit AES encryption for maximum data protection, has a no-logs policy, and protects against IPv6, DNS, and WebRTC leaks. It prevents your IP address from ever falling into the wrong hands in the depths of the internet via “Network Lock,” its kill switch available across all major platforms.
Guia Rápido: Melhores Links Da Dark Web Em 2025
- Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?).
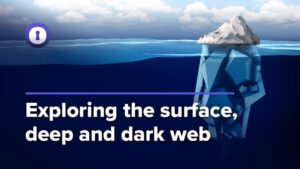
- However, Google isn’t able to find everything on the Web, as there is a deep and invisible web that is not accessible by Google.
- The emergence of search engines like DuckDuckGo has also made it possible to search on Tor as you would typically do on Chrome, Edge, and Firefox.
- Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection.
- Many people use it interchangeably with “dark web,” which is a common mistake.
- That it is an open source project that is in charge of handling suggestions and comments anonymously.
Darknet markets, their wares and services, hacking, carding, fraud, CP, and otherwise involuntary/illegal pornography are off-topic and unwelcome here. Founded in 1998 as Ixquick.com, we later changed the name to Startpage.com. At Startpage.com, they take into account the privacy dangers of recording people’s search behavior, and given their team’s strong convictions about privacy, they decided to act accordingly. Not Evil is a reflection of what the community is looking for and what the community reports as abusive or inappropriate content.
To discover content on the web, search engines use web crawlers that follow hyperlinks through known protocol virtual port numbers. This technique is ideal for discovering content on the surface web but is often ineffective at finding deep web content. Though users can upload and download digital material to its data cluster, it primarily collects data from its automatic web crawlers. However, it doesn’t work like a regular search engine, i.e., you can search content randomly. You’ll need to provide the URL of a specific Web page to access its older copies.
Is Accessing The Dark Web Illegal?
These search engines work best if you already know what site you’re looking for, not for general browsing. One option is to try DuckDuckGo’s .onion version, which is great for privacy. Other options include Ahmia and NotEvil, which focus on listing .onion links.
Encrypted Communication Tools

The Deep Web refers to web data you can’t find using a search engine like Google. Unlike the Dark Web, the hidden corner of the internet often used to conduct illicit or anonymous activity, anyone can get to the Deep Web safely using a regular browser. We’ll show you how to find information on the Deep Web and safely dip your toes into the Dark Web. These search engines are systems that list onion links from the deep web, the main task of each search engine is to allow the display of hidden pages.
Many people see hacked information and stolen card data being sold on the dark web. However, you can find legitimate content and activities here, too. For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. Blockchain even has an HTTPS security certificate for even better protection. If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites.
They know how to process the information and get it to the correct law enforcement agencies internationally. Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user. Law enforcers can use custom software to infiltrate the dark web and analyze activities. You could be monitored closely even if you are not doing anything illegal. Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims of crime may want to hide their identities from their perpetrators.