Finally, the data is purchased by consumers who use it to commit various forms of fraud, including...
vendor
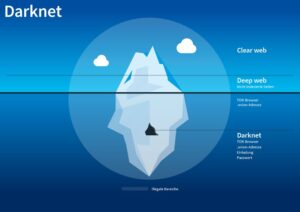
By operating in the dark web, vendors can avoid these constraints and operate with relative anonymity, reducing...
Understanding both the benefits and dangers ensures safer interaction and more informed decision-making in an ever-changing digital...
People unexpectedly have their card cloned, their identities stolen, or their accounts hacked. Most stolen card details...
They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails....