A VPN hides your internet activity, making it harder for your connection requests to be traced back to you. It’s a precaution to protect yourself before diving into the dark web. For recommendations on choosing a VPN, look for expert reviews and articles. There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks. Sites stored in the index are then ranked based on a variety of different factors, which is what decides how far up on the results page the sites appear in a search. The reason why the deep net provides this level of privacy for website hosts is that the .onion address that you use to access the website obfuscates the actual IP address of the server.
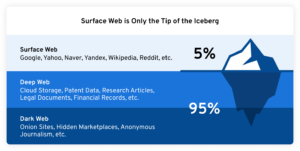
In an increasingly digital world, the internet has become an essential element of our daily lives. We rely on it for communication, shopping, learning, and entertainment. Yet, the surface internet we routinely access is only a fraction of what the web truly encompasses. Beneath the familiar websites lie layers of content that most users know little about. Among these layers, the terms “Deep Web” and “Dark Web” often surface in discussions about internet safety and privacy.
Dark Web Risks
To get on the dark web, you need a browser built for the job, and the best in the business is Tor. Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web. It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are. Due to the anonymity of the seller and buyer, these marketplaces are full of fraudulent sellers.
Managing Cyber Risk With Check Point
That groundwork was the basis for the Tor Project, which was released in 2002 and launched a browser in 2008. With the creation of Tor, users could now browse the internet completely anonymously and explore sites that were deemed part of the “dark web.” The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe. In darknet mode, you can select friends on the network and only connect and share dark web content with them. This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know.
How To Find New, Active Dark Web Links
The dark web is a small, hidden subset of the deep web that requires special tools to access. Sites on the surface web (or open web) are those visible to average users without the use of Tor or any other special browsers or software. Sites on the surface web are also indexable and can be easily found using search engines. In a classic example, the surface web can be imagined as the tip of a large iceberg whose bulk remains hidden just under the surface. You don’t need special tools or a special browser like you need to access the dark web (more about that later). Anyone can access the deep web by using specialized search engines, dedicated web directories, and other sources that can help you find the data or information.
Best Dark Web Sites 2025 – Detailed List
But it also contains other news and religious sites, private discussion forums, and medical records. You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web. So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web. In addition, the content on the pages don’t need any special or custom configuration to access. As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman.
More On How To Stay Safe On The Dark Web
Besides, governments might actively monitor such activity, and anyone showing a keen interest in the dark web can become a law enforcement target. Some of these password-protected pages (deep web) are marked with a “no-index” tag which prevents search bots from crawling them. Others (dark web) use specific protocols that the normal browsers (Chrome, Edge, Firefox) can’t connect with. It’s important to be careful when browsing the dark web; it can pose a risk as it serves as a popular hub for hackers and cybercriminals. It is crucial to exercise extreme caution when accessing the dark web. As a rule, this side of the internet hides content, identities, and locations from third parties that are common throughout the ‘surface web’ (mainstream, public websites).
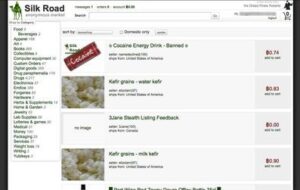
This attracted people who do illegal stuff to sell things without getting caught. One example is a website called the silk road which was on a darknet called TOR, used to sell drugs, and was taken down by the FBI. The dark web’s anonymity draws users who need private communication, want to share sensitive information, or seek access to content censored in certain regions.
Cybersecurity Threats
Most internet users access the deep web almost every time they are online. On the other hand, one cannot visit the dark web without purpose-built software. This is because the dark web is placed on darknets, an overlay network that exists ‘on top of” the regular internet. Unlike the dark web, which is deliberately obscured by layers of technology, the deep web exists just below the surface web. The majority of the deep web consists of regular websites that require users to create an account before they can be accessed.
- The dark web is a hidden segment of the internet that isn’t indexed by standard search engines.
- However, since your traffic is routed through nodes that you don’t have any control over, you are at the mercy of whoever operates these nodes.
- The advantages of I2P are based on a much faster and more reliable network.
- However, it also supports legitimate uses like protecting free speech and accessing information in censored regions.
- Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal.
- The rise of cryptocurrency, and in particular Bitcoin, significantly increased the dark web’s use in illegal trade.
RiseUp is a top dark web website that offers secure email services and a chat option. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. The platform is protected from government interference and malicious attacks to protect the user. In addition, it ensures that no record of communication is stored. The darknet is a network, and the deep web constitutes the chunk of the World Wide Web that is beyond the reach of the search engines. So, we can decipher the dark web as the World Wide Web of the darknets like Tor, Freenet, etc.
Find Out Which Of Your Users’ Emails Are Exposed Before Bad Actors Do
It can only be accessed through special networks like Tor or via static IPs shared privately. Technical considerations here involve encryption strength; weak implementations undermine the very privacy this layer seeks to protect. The Deep Web thus balances safeguarding data with the practicalities of access, a dynamic critical to modern digital operations. It’s quickly been adopted by criminals to shuffle illegal content and communication around the world. In combination with the rise of cryptocurrencies, the dark web has enabled billions of dollars in illegal trade.
This technique is ideal for discovering content on the surface web but is often ineffective at finding deep web content. It is also worth mentioning that it is believed that the NSA hosts a large number of entry and exit nodes into the dark web. The good news is that there is a much faster version of privacy technology that is similar to Tor, albeit much faster. A VPN is a technology that (like Tor) provides you with a string layer of encryption to stop local networks, ISPs, and government agencies from being able to monitor your online activities. To access the purposely hidden part of the internet, you have to use special tools such as the Tor browser.
- ExpressVPN had created a .onion version of its website to allow greater privacy and anonymity for Tor browser users.
- You may encounter fake marketplaces promising illicit goods or services but delivering nothing after payment.
- Attackers can use tools like keyloggers to gather your data, and they can infiltrate your system on any part of the web.
- In reality, there’s nothing inherently dangerous about accessing either, and doing so is surprisingly simple.
It includes legitimate resources such as academic databases and private networks, as long as users respect privacy laws and do not engage in unauthorized activities. The dark web is a subset of the deep web that requires special software, like the Tor browser, to access. Known for its focus on anonymity, the dark web is often linked to illegal activities, although it also serves as a platform for privacy advocates and journalists in repressive regimes. There are also discussion forums, hacking communities, and message boards focused on topics ranging from cybersecurity and cryptography to more disturbing and illegal content.
Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor. The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web). The deep web is basically all the content that you can’t find using Google or Yahoo search. Pixel Privacy believes in digital privacy and does not believe in using it for heinous and/or illegal activities, and so the focus of this article will be on legal activities. Sure, it’s not as secure as the clear web version, but it’s there and totally legal to use.