It’s an especially essential tool for researchers and historians looking to track the evolution of websites over time. Its advanced search feature makes it one of the best darknet search engines. You can use advanced search feature to customize the searches to narrow down the search as per your need. Anyway, as a darknet search engines (this is quite literally GDark’s tagline), it’s pretty active. This article and list of dark web search engines is purely and solely meant for educational purposes.
Adamant offers blockchain-based secure messaging without needing phone numbers or email addresses. The platform stood out during my testing for its commitment to anonymity — all messages are fully encrypted and stored on a decentralized network. It’s particularly useful for sensitive communications that need to remain private. TorLinks maintains one of the most reliable directories of verified .onion sites.
Other Privacy Tools And Services
- Hidden deepweb search engines can be a valuable tool for researchers, journalists.
- Instead, you need to use specialized tools and techniques to access them.
- Also known as Not Evil, this dark web search engine offers access to a wide array of .onion content.
- These practices not only safeguard your personal information but also enhance your overall browsing experience.
- The easiest thing to do to maximize your online safety is to install a VPN.
They know how to process the information and get it to the correct law enforcement agencies internationally. Many services that are allegedly offered on the dark web are scams. Some services are genuine; you can get what you want at an agreed fee. It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals. Be sure that your experience with Whonix will be comparable to Tor because both programs share the same source code. The Invisible Internet Project’s distinctive feature is its ability to use decentralized file storage with the help of the Tahoe-LAFS plugin.
This marked the beginning of efforts to explore the vast, unindexed parts of the internet. Early tools for deep web exploration were limited in functionality. They often required users to manually navigate directories or rely on basic search protocols. For example, in 2005, Google introduced the Sitemap Protocol, which allowed search engines to crawl deeper into websites. This innovation made it easier to access hidden content, though it still fell short of fully unlocking the deep web.
Secure Your Connection
It will also generate a great service list of the plug-ins that the website is currently using, its frameworks, and even its server information that’s publicly available. It’s another great tool for red and blue teams in initial server recon as part of a security audit. A secondary function of OSINT tools these days is to find ‘extra’ relevant information outside of the direct query that you have looked for. Such information could be an acquired company, a secondary company, or close relationships or contacts with the target in question. This can identify further potential physical address locations of the target.
PageOn.ai’s intuitive interface makes it easy to navigate and utilize these tools, ensuring a seamless user experience. Additionally, the anonymity of the invisible web attracts cybercriminals. Activities like data leaks, fraud, and money laundering are common.
Stay Private And Protected Online With A VPN
You are not required to provide your personal information to create an account. The email service is available both on the surface and on the dark web. The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live.
Are Onion Sites Safe?
This makes it impossible to track down the physical server under ordinary circumstances. With how mythologized the deep web and dark web have become, you’d be excused for thinking it’s difficult or dangerous to access. In reality, there’s nothing inherently dangerous about accessing either, and doing so is surprisingly simple.
Domain-Based Search Engine Evaluation
The victim can access this onion.ly website with their regular browser. When choosing a deep web search engine, start by identifying reputable providers. Reliable search engines often have a history of consistent performance and positive feedback from users. They prioritize your safety by offering secure connections and trustworthy results.
The Best Dark Web Links (Tested & Working In
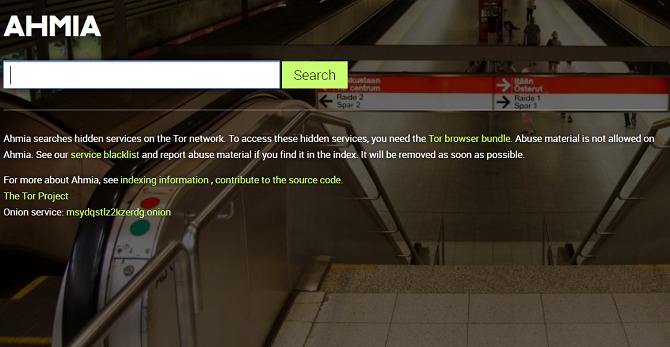
It will give you more results than you’ll find on Google and doesn’t order or filter what you find based on advertising. Torch is one of the oldest and most well-known dark web search engines, providing access to a vast index of .onion websites. Unlike many dark web search engines, Ahmia is accessible on both the surface web and Tor, allowing broader access to its indexed content. Onion sites, also known as Tor sites, are web pages with the “.onion” suffix, accessible only through the Tor browser.
The use of the dark web raises suspicion as it shows there is something you want to do privately. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data.
How The Deep Web Is Different From Traditional Internet
Using the dark web poses risks, making a VPN essential for privacy. Forest VPN provides strong encryption, keeping your online activities anonymous. Whenever you venture into the dark web, using a VPN like Forest VPN is crucial. A VPN encrypts your internet connection, hiding your IP address from potential hackers and prying eyes. Forest VPN offers a seamless experience with no data logging, ensuring your privacy remains intact.
Most of us spend our time online bobbing around at the “top” of the web. This is called the “surface” or “open” web and it’s where we can engage with various online services, including e-commerce sites, news sites, blogs, personal websites, and social media. The online content that is easily visible to us and the search engines we use, forms the tip of the web iceberg. Below this virtual water line comes the online content that is non-indexed and can’t be accessed via standard search engines.
- Any and all of your actions, on and forward any of these search engines/websites, is 100% your own responsibility.
- While it may not be a traditional deep web search engine, it is the gateway to the repository of all public domain information and services.
- However, unlike other search engines, DuckDuckGo doesn’t personalize your search results based on your past search history or browsing behavior.
- Another great source to find and explore dark web marketplaces or other sections is to visit Reddit’s resourceful forum.
What Is The Deep Web And How Do You Access It In 2025?
And they may ask for personal information such as your name, email address, and physical address. This information can be used by hackers and cybercriminals to steal your identity or perpetrate other crimes. One of the advantages of using Candle is that it has a user-friendly interface that makes it easy to search for specific content. It also provides users with an added layer of anonymity, which can be important when accessing content on the Dark Web. It is an open-source search engine that is designed to be anonymous and secure.

It might sound weird that Google doesn’t index these pages, but it does carry some logical sense. Google’s purpose is to show the most relevant information to all of its users quickly and easily. That means that Google wants to minimize the amount of time users spend searching for certain queries. Reddit is actually available on the dark web now, so there’s no need to rely on third-party tools to access it via Tor.