Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. It is the most common way, and it requires one to have a browser that supports the Tor protocol. Some web browsers that utilize the Tor protocol include the Tor browser, Brave, Onion browser, Firefox, and Chrome. More importantly, you should now know how to access these hidden sectors of the internet at your leisure.
Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows. For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions. Therefore, the legality of the dark web will mainly depend on how you use it.
The Hidden Wiki

To get on the dark web, you need a browser built for the job, and the best in the business is Tor. Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web. It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are. In 2023, attackers distributed fake Tor Browsers with trojans through phishing pages. After installation, verify the file’s authenticity using PGP – the instructions are on Tor’s website. If you’re new to PGP, spend 20 minutes learning it – it could save you from malware.

Different dark web search engines cater to various needs, offering varying levels of privacy, security, and ease of use. Torch is one of the oldest dark web search engines, having served the darknet community for years. It boasts a vast archive of over 400,000 pages, providing comprehensive coverage of .onion sites, including forums, blogs, and marketplaces.

Does Tor Hide Your IP Address?
This technique is ideal for discovering content on the surface web but is often ineffective at finding deep web content. Deep web browsers are programs or applications that allow access to non-indexed websites. Each browser interprets information from different types of files and onion sites on the deep web. In addition, it allows you to visit onion websites and do activities within the deep web. In other words, link one site to another, print, send and receive mail, among other functionalities. It doesn’t track browsing habits or personal data and won’t expose a user’s identity or location.
Onionname
They are a kind of guide or indexes of pages and internet websites, sometimes with a short description of each site they recommend. While you’re at it, now might be a good time to check whether any of your personal information has been leaked on the dark web. ProtonMail is an email service that uses end-to-end encryption, making your email accessible to you and only you. The service retains no copies of any data that passes through a ProtonMail account. Although ProtonMail also exists on the clear web, accessing it via Tor provides an extra layer of privacy if you don’t want to leave a trace of you even using ProtonMail.
How To Safely Access The Best Dark Web Sites – Quick Guide
It’s maintained by a volunteer-run collective from the USA that protects the platform from malicious attacks and pledges to support social justice and progressive causes. Riseup’s secure email and chat help individuals communicate without fear of surveillance or data interception. ProPublica is a non-profit investigative journalism outfit based out of New York City. It’s committed to transparency and public service, which is why it maintains a dark website along with its site on the surface web. Your IP is still being revealed to one of the nodes in the onion, meaning your activity and identity can be unmasked. Of course, bypassing paywalls is ethically questionable and may be illegal in some jurisdictions.
Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile. Cryptocurrencies such as Bitcoin have been the dark web currency even before they became available to the general public.
Navegue Tranquilamente Na Dark Web E Sites onion Com Uma Boa VPN
- If this sounds similar to The Wayback Machine, the concept is indeed the same.
- They often required users to manually navigate directories or rely on basic search protocols.
- Primarily favored by individuals interested in procuring illicit goods and services from Dark web markets, Candle provides a straightforward and minimalistic user interface.
- It works by sending internet traffic through volunteer-operated nodes all over the world.
Project Gutenberg offers over 70,000 free ebooks for you to check out and download. It provides variable formats and a list of similar books to download. It’s undoubtedly one of the best sites to download ebooks for free. The current repository has over 20,000 journals with over 10 million articles across all subjects. Although you can easily find free articles on Google Scholar, and it can access some of the information, we think that the DOAJ is a better research tool. Not everything on the web will show up in a list of search results on Google or Bing; there are numerous places that the sites’ web crawlers cannot access.
- It encrypts your traffic at the entry node and changes your IP address.
- DuckDuckGo is a reputable US-based software company, so their Tor site itself is safe to use.
- To protect your data from the websites you visit, one of the most effective steps is to hide your IP address, which can reveal your location, identity, and browsing habits.
- Dark web forums are online communities where individuals participate in discussions on a wide range of subjects, from technology and privacy to more illicit matters.
- As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls.
Just Another Library
To maximize LibreY’s potential, access it through the Tor browser for enhanced security. Use specific keywords to refine your search results and avoid wasting time on irrelevant pages. If you’re conducting research, focus on academic databases or forums indexed by LibreY. Bookmark frequently visited services to streamline future searches. Always verify the legitimacy of the sites you visit, as even privacy-focused search engines can occasionally index questionable content.
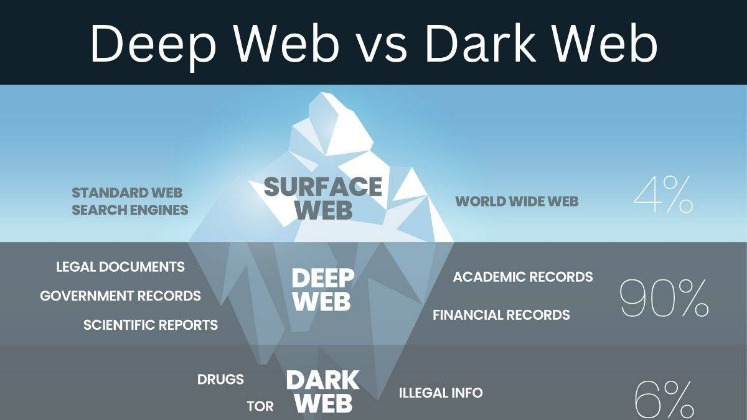
You can’t use Google to access the Deep Web—you’ll need to go directly to websites and archives to find non-indexed files, or try a Deep Web search engine. Unlike the Dark Web, which requires a special web browser called Tor, you can use any browser to get to the Deep Web. It’s very easy to click on something and go down a rabbit hole of the Internet you probably don’t want to visit. We do not recommend venturing into prohibited, unethical sites on the Dark Web. When you find nasty content, just close all the windows, and Tor will erase your records. If you’re worried about the searches you’ve done on Google, learn how to delete your Google search history.
Some markets are relatively short-lived (thanks to law enforcement), but others are notorious enough that they survive, for instance, Silk Road, AlphaBay, and Hansa. It allows you to search for images, maps, files, videos, social media posts, and more. It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications.
The extensive nature of the deep web makes it very difficult to bring to light the exact pages and websites active at any one time. You should also evaluate the security features of your chosen tools. Look for search engines that prioritize encrypted connections and avoid tracking your activity. These features enhance your privacy and protect your data from being intercepted. If a search engine lacks these safeguards, consider switching to a more secure option. Additionally, advanced security measures prevent your search history from being tracked.
Tor Search is a very efficient search engine because it indexes new content all day from the TOR network. As we enter 2025, these tools are adapting with improved security and functionality to meet user needs. Renowned for its precision, it offers highly accurate and relevant results, making it a trustworthy resource for dark web users. This is especially beneficial for professionals in cybersecurity or research, who require quick access to specific types of information.
Blockchain.com’s impact on the cryptocurrency community extends beyond its products and services. The platform has been an invaluable resource for data and analytics, offering detailed insights into blockchain activity, including transaction volumes, wallet activity, and network health. Researchers, investors, and enthusiasts rely on Blockchain.com’s data to understand market trends, making informed decisions based on comprehensive blockchain information. While other dark web browsers (like Brave) can support onion links, the Tor Browser is highly recommended because it’s preconfigured with security and anonymity features optimized for the dark web.