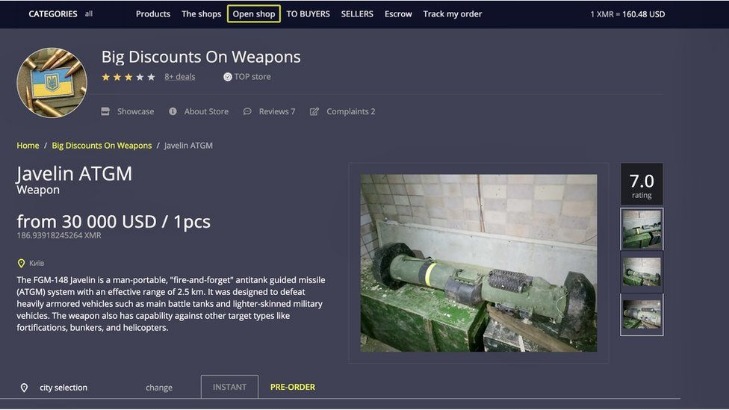
This growth demonstrated the demand for an anonymous marketplace and showed the world how cryptographic tools could be used for illicit activities. But in addition to the marketplace, darknet participants also need an untraceable payment method in order to maintain maximum confidentiality in their activities. Silk Road was the first darknet marketplace to use the anonymity of cryptocurrencies for payment, thus paving the way for today’s underground world of dark web marketplaces to follow suit. Like in legitimate economies, pricing on the dark web reflects a dynamic interplay of supply, demand and competition. These examples illustrate typical pricing for common items and services available in dark web markets.
Fortify Your Mobile Protection: Building Customer Trust With Advanced Security

One of the most notable markets is PhantomX, which has gained popularity for its robust escrow system and multi-signature wallet integration. This ensures that funds are only released once both parties confirm the transaction, significantly reducing the risk of fraud. Additionally, PhantomX employs a decentralized hosting model, making it resistant to takedowns and ensuring continuous availability. No, visiting dark web sites is not illegal, but engaging in illegal activities there is.
Is Claude Safe And Secure In 2025?
Since the 1970s, illicit trades have thrived on the internet, but they require in-person exchanges. Dark web markets flourished, starting with the Silk Road in 2011, pioneering the use of Bitcoin (BTC). Torrez has been steady since 2020, rocking 4,650+ listings with BTC, LTC, ZCash, and Monero. Wallet-less payments and multi-signature deals make it a safe bet—I’ve never worried about getting burned, even after a close call with a dodgy vendor once.
Ways Small To Midsize Businesses Can Stay Safe In The Cloud
The Dark Web presents significant cybersecurity risks for businesses, as stolen credentials, intellectual property, and sensitive data are frequently traded on illicit marketplaces. Cybersecurity professionals actively monitor these underground forums to identify leaked corporate information, using automated web crawlers, threat intelligence platforms, and Dark Web monitoring services. This approach enables businesses to conduct cybersecurity risk assessments and mitigate potential threats before they escalate into financial losses or compliance violations. Today, darknets are populated by a vast array of users, ranging from privacy-conscious individuals to cybercriminals, hacktivists, and nation-state actors.
Illegal Pornography
They could get a batch of bad products, get arrested before they can ship your order, or any other number of things. There’s no guarantee that placing an order with any DNM vendor will be safe or shipped. Functionally, accessing DNMs and using them requires quite a few extra steps to protect the anonymity of the buyers, sellers, and server admins. To get into DNMs, you’ll likely have to figure out the basics of things like PGP encrypted messages and using the TOR browser. TOR Browser is a free, modified version of the Firefox web browser configured to connect to the TOR network. The dark web hosts a variety of illegal activities, many of which fuel cybercrime and real-world harm.
Related Articles From The Business Security Section
DarkMarket’s thirty-four-year-old founder and administrator was apparently an Australian man, who was arrested last weekend near the German-Danish border. The police referred to him only as Julian K. Shortly after Julian K.’s arrest, DarkMarket was shuttered by the German police. On the site, a graphic appeared, showing an insect with a female face—a logo for DarkMarket—underneath a flyswatter. Notably, postsoffering Redline stealer logs, a popular malware family, tripled from anaverage of 370 per month in 2022 to 1,200 in 2023.
The darknet in 2025 is a thriving, evolving ecosystem of anonymous marketplaces accessible via Tor. Driven by demand for privacy and illicit goods, these top 10 markets—featuring Alphabay, Archetyp, and more—offer unparalleled variety, security, and resilience despite law enforcement crackdowns. This guide provides verified .onion links, market stats, and expert insights into Tor and Monero usage as of February 21, 2025.
Frequently Asked Questions (FAQs) About Dark Web Marketplaces
I2P can only be used to access hidden sites that are only available on the I2P network. But remember, it’s essential to take all the necessary and important security steps before entering such sites on the dark web. As mentioned before, your ISP and government institutions are not able to see what sites you visit on the Tor network, but they can probably see that you use Tor. Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites. The majority of the users on the dark web use the Tor (The Onion Router) browser.
Seller-to-seller Network
Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP. It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products. Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web. Quality and validity of the data it provides justify its higher cost over other marketplaces. The platform’s popularity continues to grow, attracting both new and returning customers. To expand their reach, some marketplaces established parallel channels on Telegram.
Now, that is not to say illegal behavior is completely beyond detection. The dark web combines encryption, anonymity, and hidden doorways to provide the perfect sanctuary for such illicit activity compared to the usual internet, which is more vulnerable and trackable. Of course, not all the popular and widely-used dark web sites and things like marketplaces on the dark net are illegal.
It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in.
- Beyond legal requirements, businesses bear an ethical responsibility to safeguard the sensitive data of their customers and employees.
- Addressing these risks requires a proactive approach that combines technology, education, and strategic planning.
- Archetyp launched in May 2020 and quickly grew to become one of the most popular dark web markets with an estimated total transaction volume of €250 million (A$446 million).
- As these marketplaces evolved, so did the challenges for security professionals, who now face a constant battle to keep up with ever-changing tactics used by criminals.
- If the buyer or seller gets caught, there are significant legal ramifications.
The stolen data included names, contact information, and order histories. Dark web listings surfaced almost immediately after the breach, advertising this information for sale to cybercriminals. An award-winning cybercrime threat intelligence firm, KELA’s mission is to provide 100% real, actionable intelligence on threats emerging from the cybercrime underground, to support the prevention of digital crimes. We continuously monitor underground markets for the emergence of new “cryptors,” which are tools specifically designed to obfuscate the code within malware samples. The primary purpose of these tools is to render the code undetectable by security software. In 2024, our expert observations indicate that commercial advertising for these cryptors have indeed gained momentum.
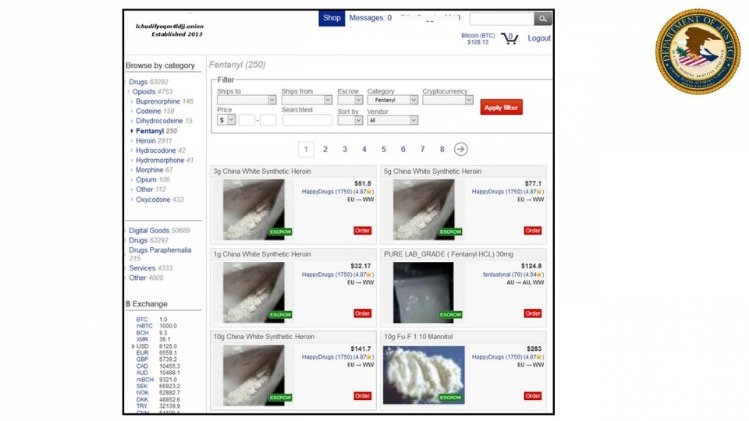
Over the next two years, the Silk Road set the standard for darknet marketplaces. By the time it was shut down in October 2013 and Ross Ulbricht arrested, the site had traded an estimated $183 million worth of goods and services. Darknet marketplaces emerged around 2011, with Silk Road setting the standard for how these platforms operate. Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers.