Technically, yes, but you’ll still need to use the Tor network to access .onion sites, even on Chrome or Firefox. Chrome offers proxies that can give you access to dark sites, while you need to change the configuration of Firefox to do so. However, these methods can compromise your online security and would be very slow, so it’s better to just use Tor. No, simply entering or browsing the Dark Web itself isn’t illegal in most countries.
- It publishes a newsletter in multiple languages and not only runs onion services for its website but all its email and chat services.
- A host is basically a website’s house, or where it lives and takes up space.
- Deep Search Engine is a darknet search engine that promotes known scams on the Tor network.
- It’s a part of the internet that’s less regulated and more shadowy, for better and for worse.
- These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private.
How Do I Find onion Links For Sites?
Considering how regularly dark web sites vanish and go offline, it’s better to have more than one source to help you find .onion URLs. Mail2Tor makes a good alternative as it allows users to send/receive messages anonymously through webmail or an email client. What’s more, all mail is secured using encryption, and the provider doesn’t store your IP address either. Though Facebook knows a lot about you than you can imagine, it isn’t keen on sharing this data with others. The social media giant has also been the target of censorship from repressive governments time and time again.
MICROSOFT SECURITY TOOLS

It became the blueprint for other dark web marketplaces that tried to take its place. Ulbricht faced several serious charges, including distributing illegal drugs, running a criminal enterprise, hacking, trafficking fake IDs, and money laundering. In the end, he was sentenced to life in prison for running one of the largest and most scandalous dark web cases in history. If for any reason, you decide to visit these hidden corners of the web, ensure you at least study and understand the common traps. Getting familiar with the tactics scammers use will go a long way in helping you protect your online data and assets.

Unlike Ahmia and Haystak, however, DuckDuckGo doesn’t search .onion sites. Use it to search the normal internet from the privacy of your Tor Browser. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts.
Legitimate Use Cases For The Average User
The integration of cryptocurrencies like Bitcoin and Monero continues to provide unparalleled anonymity, making these markets a preferred choice for buyers and sellers alike. TorLinks is a robust Dark Web directory that offers a compilation of links organized into commercial and non-commercial categories. Each category is further divided into multiple sub-categories for easy navigation. Initially launched as a backup of The Hidden Wiki, it’s now the primary go-to resource for accessing .onion sites and resources when other directories face unexpected downtimes. To help you avoid these issues, my team and I tested dozens of .onion sites and found the best ones that provide uncensored access to information while keeping you anonymous online.
Like any other crypto wallet, you can trade Bitcoin using Hidden Wallet. But unlike other wallets, you don’t have to worry about your personal information being leaked since it’s hosted on the Tor network. Hidden Wallet promises bank-grade security for your Bitcoins and claims that it can never access your keys or crypto funds.
Use A Trusted VPN

These advancements will further solidify their position as a secure and reliable option for users worldwide. It is a private search engine that lets you search the regular internet via Tor. This allows you not only to visit sites with the added privacy provided by the Tor network, but also search the web as privately as possible from inside the Tor browser.
Is It Illegal To Enter The Dark Web?
- These discussions are not only theoretical but also practical, offering insights into setting up laboratories, enhancing production efficiency, and adhering to safety protocols.
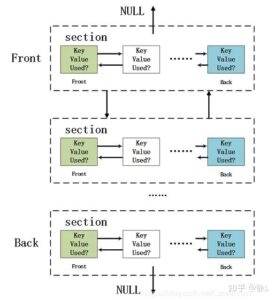
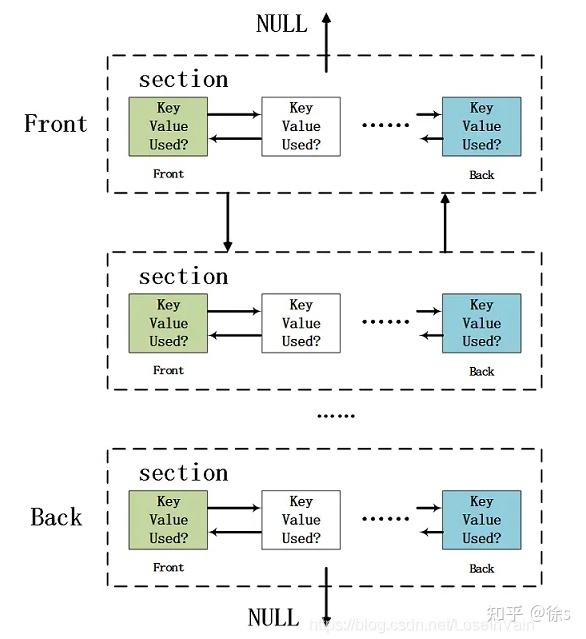
- The encryption technology routes users’ data through a large number of intermediate servers, which protects the users’ identity and guarantees anonymity.
- The buyers, or “consumers,” are cybercriminals who use these tools to launch illegal activities.
- If you are in a position to report the incident safely, you should report it to the authorities immediately.
- Its intuitive interface and advanced search features make it easy to find local and global products.
But accessing this hidden part of the internet safely requires reliable Dark Web search engines — tools that help you explore the darknet without compromising your identity or security. Using a reliable VPN like ExpressVPN with dark web search engines is essential for protecting your privacy. It hides your IP address, encrypts your internet traffic, and prevents your activity from being traced. A VPN also masks your online behavior from ISPs, which could flag you as suspicious for accessing the dark web. This added layer of security keeps your identity hidden and shields you from online threats. Since regular search engines don’t index .onion sites, finding what you need on the dark web can be tricky.

New Shamos Malware On Mac: Beware Of ClickFix Attacks
DefCon, ProPublica, the CIA, various libraries, and open-source software providers also feature in this area of the internet. The Tor network is operated by thousands of volunteers worldwide who maintain the proxy servers that protect your identity. You can download the Tor Browser for Windows, MacOS, Linux, and Android. A VPN will mask your location and stop the online breadcrumbs that can lead back to you. Connections made while a VPN is active will also be encrypted, helping you stay protected from eavesdropping and man-in-the-middle attacks.
Besides, victims of crime may want to hide their identities from their perpetrators. Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web.
What Are Tor Websites Or Onion Websites?
It’s important for users to approach with caution, as the dark web can host content and services that are illegal or harmful. The Hidden Wiki itself does not host content but acts as a conduit to other sites. You face significant risks when using dark markets, including scams where vendors take payment without delivering goods. There’s high exposure to malware and cybersecurity threats that can steal your personal information. Law enforcement agencies actively monitor these markets and can track users despite anonymity measures.
It also offers a comprehensive list of marketplaces, exchanges, and websites linked to fraudulent activities, helping you stay informed. LifeLock Standard helps safeguard your personal information, accounts, and identity. Dark web forums typically look like run-of-the-mill message boards. The real difference lies in what you can post and the poster’s anonymity.
Ahmia’s .onion link is a search engine that indexes hidden services on the Tor network, allowing users to find .onion sites safely and efficiently. It filters out harmful and illegal content, focusing on legitimate resources and services. Ahmia has become a trusted tool for navigating the Dark Web, with thousands of users relying on it for its transparency and user-reporting features. These onion websites are specifically designed to be accessed through the Tor network, a free and open-source software for enabling anonymous communication. The “onion” in their name refers to the multiple layers of encryption that protect user identity and activity, much like the layers of an actual onion.