DNMs have a limited life and may be shutdown suddenly, leaving users with unfulfilled orders and sellers with no means of communication. The .onion top-level domain (TLD) name is the dark web’s version of “.com” or “.net”. Any site that ends with .onion can only be accessed through TOR. Unlike traditional TLDs, servers using the onion TLD are more difficult to locate. This makes it more difficult for authorities to locate and take down these sites. The Onion Project, or TOR is the predominant anonymous computer network.
Risks Posed To Small Businesses

If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security. The dark web is a part of the internet that you only step into with a specific tool (Tor, more on this later in the article). Though people usually think of dark websites as the wrong online place, that’s not the complete truth.
Common Scams And Fraudulent Activities On Darknet Markets

These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It assigns a task to the client instead of the server, eliminating server-related vulnerability.
Making Cybercrime Easy For Anyone
(inPixel) For more information on parental controls, please visit the official Minecraft website. It highlights the variety of goods that can be sold and the methods which they use to ship these goods worldwide. It also gives insight into how the vendors operate and how they explain their products and the reviews that they receive.
We The North Market (Best For Secure Transactions & Low Fees)
In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet. This was the initial framework for anonymous communication and file sharing. Even after Silk Road went down, dark web marketplaces haven’t slowed down. Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement. They sell these files for just a fraction of the original cost on the surface web or even share freely, which makes them tempting for people looking for shortcuts.
Is There A Future For Dark Web Marketplaces?
A network browser gives you access to sites with the ‘.onion’ registry operator. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. It relies on P2P connections and requires specialized tools and software. Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship.

The Best Dark Web Markets To Consider In 2025
Like other marketplaces, ASAP Market also requires you to register for an account. The marketplace has several rules that every user is bound to follow. If any user is found not complying with the law, strict and immediate action will be taken against them. It uses PGP encryption to protect sensitive data and messages, and accepts payments via Monera and Bitcoins to keep you anonymous on this marketplace. Vice City Market is a new and cutting-edge dark web marketplace where you can find a range of products and vendors at an affordable price (compared to the damage they do to the victims). To access this marketplace, you must register, but before that, you must verify yourself as a human by passing a CAPTCHA test.
Tor2door Market

Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2024. There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. Security is an ongoing process, and staying updated on the latest threats and security practices is crucial for maintaining the integrity of your apps. One of the biggest problems cybersecurity teams face isn’t a lack of tools — it’s too many alerts.
- The DarkShades RAT (Remote Access Trojan) is malicious software designed to compromise and control a target device, often a computer or a mobile device.
- Users favor marketplaces with straightforward navigation, efficient search functions, and clear product categorizations.
- Despite its name, the marketplace operates primarily in English and serves a global audience.
- Encourage users to download apps only from official app stores, regularly update their devices, and be cautious about granting excessive app permissions.
- Thanks to the VSCode team at Microsoft for creating such an excellent code editor.
- This means the server admins must pay significantly higher hosting fees than they would on the clearnet, for less reliable service.
Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals.
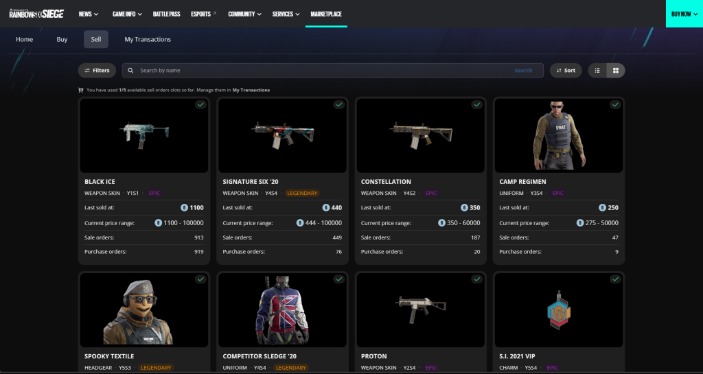
Product Details
Businesses face substantial cybersecurity risks due to the proliferation of these marketplaces. Data breaches often lead to sensitive corporate information appearing on the dark web, which can fuel further attacks. A security gap analysis can help businesses identify vulnerabilities that hackers exploit to compromise their data. Additionally, investing in cybersecurity services for small businesses ensures stronger defenses against threats originating from these illicit platforms.
The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web. However, you can find legitimate content and activities here, too. For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies.
The story of dark web marketplaces kicks off with Silk Road, launched in 2011. It was the first big site where people could anonymously buy drugs using Bitcoin, and it gained a lot of attention, until it was shut down by the FBI in 2013. This case demonstrates how proactive measures could significantly mitigate the risks posed by dark web activities.