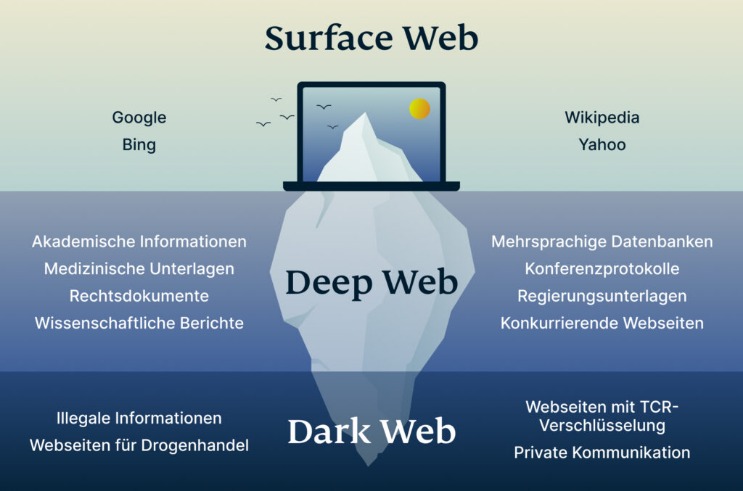
Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome.
People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. The biggest and most frustrating part about dark websites is that they live for a short span of time. These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies. Using the ProtonMail .onion site offers security and privacy advantages. Moreover, the company also uses HTTPS and SSL encryption on the Onion site for extra protection. This makes it even harder for third parties to see your email traffic.
Was Ist WPA2 (Wi-Fi Protected Access ?

They can be easily traced and even prosecuted if they share the information on the surface web. SecureDrop is a site that protects the privacy of journalists and whistleblowers. SecureDrop is a dark web link that allows whistleblowers on the dark web to communicate and share information with journalists safely and without being tracked.
Orbot: Tor Für Android
As we stated earlier, the Hidden Wiki is an unreliable platform. Blockchain.info (now Blockchain.com) is a popular cryptocurrency wallet and blockchain explorer service (one of the first sites to launch on the dark web). It was initially created to provide additional security and eliminate cryptocurrency theft. It’s a wallet, explorer service, not a dark web marketplace itself, but still a helpful resource. Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal. Facebook’s dark web version allows users to access the site where it is banned or restricted.

It’s recommended not to be too vigilant here and leave the investigation to the professionals. Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments. Additionally, you can opt for Subgraph OS as a second option to Tor. Be sure that your experience with Whonix will be comparable to Tor because both programs share the same source code.
Der Tor Browser: Anonym Surfen Mit Legalem Zugang Zum Darknet
The threat can extend to your entire network of devices connected to the internet. Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons.
Brauche Ich Ein VPN, Wenn Ich Tor Verwende?
If you don’t take the necessary measures, many unsavory activities can expose you to unnecessary risks. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. Just like Google, the dark web has some search engines present on it. Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results. Hence, you never know when a popular .onion site is going to vanish, or even die.
Was Ist Ein Cloud Access Security Broker?

This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime. Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023. Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it. Join millions of users who trust ForestVPN for privacy and unrestricted internet access. The US government created the dark web to help its spies communicate and exchange information securely.

Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though). The best thing is to actually understand how to find the fresh, new links. You only need to upload your PGP key or let the platform create one. Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile.
- I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web.
- An easy way to find content on the dark web is to receive a link from someone who already knows about it.
- While this is not much compared to standard email services, it is enough for PGP-encrypted messages.
- The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data.
- This .onion link makes it impossible for hackers to impersonate your profile.
- The US government created the dark web to help its spies communicate and exchange information securely.
A Quick Guide On How To Use A VPN With Tor
Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. The anonymity provided by onion routing comes at the cost of slowing your internet considerably.
- With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential.
- We review and list tools and products without bias, regardless of potential commissions.
- Whether you’re looking to enhance your cybersecurity knowledge or stay informed about dark web activities, our platform is your trusted source.
- In addition, it ensures that no record of communication is stored.
- This means you have to know someone who is already using the platform.
- This adds extra protection since opening Tor itself encrypts your traffic.
Marketplaces For Everything Illegal
An easy way to find content on the dark web is to receive a link from someone who already knows about it. These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. This .onion site is a bit different from the others reviewed above. The Imperial Library is a dark website with many digital books. Wasabi is one of the most popular cryptocurrency wallets on the dark web.
Potenzielle Malware
You could be monitored closely even if you are not doing anything illegal. The use of the dark web raises suspicion as it shows there is something you want to do privately. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. Think of Tor as a regular browser like Firefox, Google, or Safari.
Use A Secondary Non-admin Account
For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions. Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims of crime may want to hide their identities from their perpetrators. Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble. Remember that illegal activities can still incriminate you, whether you are using a Tor browser.



