Many news publications, like the ones listed above, have a SecureDrop on their .onion sites. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet. However, it’s much harder to get at the people who are doing the uploading and downloading.
It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage. The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic at the entry node and changes your IP address. This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously. ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe.
Shuttered Dark Web Marketplaces
DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia. Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs. For example, the deep web is often a platform used by political activists who own a blog. But it also contains other news and religious sites, private discussion forums, and medical records.
Cypher Market
In addition to counterfeit merchandise, MGM Grand Market offers access to stolen credit card information, compromised bank accounts, and other financial fraud-related services. There are many clear, deep, and dark web sites, forums and marketplaces where threat actors can access victims’ online accounts. In addition, encrypted messaging platforms like Telegram and QQ provide a safe haven for communications about malicious acts and are, therefore, popular among threat actors. Shadow Market is one of the largest English speaking marketplaces specializing in selling stolen credit cards, credit card dumps with full info such as Track 1 and 2 code, all billing info and CCV2.
Does The CIA Have An Onion Site?
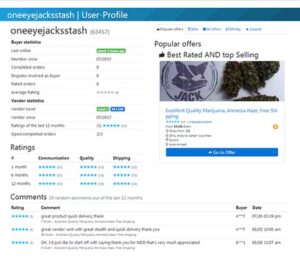
We consider the things you ought to check before making your decision. We rank markets based on what we believe is important for you and let you choose what works for you best. The BBC’s international edition Tor version is available on the dark web, giving access to unbiased news in regions where the BBC is blocked or censored.
- The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero.
- That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy.
- Sometimes, you might be hacked by using weak passwords or even just connecting to unsecured Wi-Fi on public networks.
- This proven technology, seamlessly working in the background, analyses transaction data and authenticates users in real-time, ensuring only legitimate transactions proceed.
- The Tor browser allows you to browse the internet anonymously and visit inaccessible sites.
Awazon Market

“The most important thing is for people to keep an eye on their transactions and report any fraud immediately,” Krebs says. Unless you live the rest of your life only paying with cash, you’ll never be totally impervious to payment fraud. On April , the Genesis market was seized as part of the international law enforcement crackdown dubbed “Operation Cookie Monster”. The site had specialized in the sale of “browser fingerprints”.

How To Access Onion Sites

Tor Browser prevents someone watching your connection from knowing what websites you visit. All anyone monitoring your browsing habits can see is that you’re using Tor. As we mentioned above, when you connect to Tor your data first goes through an entry node, which can see your IP address. By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity. This means that using the dark web may attract attention from your ISP or even law enforcement.
The Tor browser is the most preferred browser for surfing the dark web because it creates encrypted pathways for user traffic, ensuring all the activities are anonymous. The dark web is not easily accessible, especially with browsers like Chrome or Safari, as it requires specialized protocols like Tor’s onion routing. As a result, the recommended browser for accessing the dark web is the Tor (The Onion Router) browser. So, whether you seek refuge from oppressive regimes, are searching for answers to hard or embarrassing questions, or are trying to share confidential information securely, there is something for you.
Best Onion Sites By Category
A network browser gives you access to sites with the ‘.onion’ registry operator. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc. Other sites explicitly block search engines from identifying them. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship. It works by sending internet traffic through volunteer-operated nodes all over the world. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites.
Best Dark Web Sites 2025 – Detailed List

Knowing this, we tested many dark websites, and only the safest and most reliable ones made it to our list of 29 best dark web sites you should know in 2025. Having trouble deciding what dark web sites are safe and reliable? Markets that lack proper security often become targets for law enforcement, scammers, or cyberattacks.
While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. It’s impossible to access the dark web with a regular browser like Chrome or Safari. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy. The compromised Tor exploit might trace back to you, but then again, your VPN will lead it somewhere else – which makes it impossible to be traced back to you. But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network. It’s not a secret that ISPs (Internet Service Providers) and the FBI are tracking Tor users.
- Make sure that when you download the Tor file, it’s from their official website.
- Comparitech researchers gathered listings for stolen credit cards, PayPal accounts, and other illicit goods and services on 13 dark web marketplaces.
- ExpressVPN had created a .onion version of its website to allow greater privacy and anonymity for Tor browser users.
- Russian Market has consistently remained one of the most popular and valuable data stores on the dark web.
- Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook.
They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk. But these efforts of law enforcement don’t go in vain; hackers and criminals lose trust if a website or marketplace goes down. It became the blueprint for other dark web marketplaces that tried to take its place.
Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. Some markets are relatively short-lived (thanks to law enforcement), but others are notorious enough that they survive, for instance, Silk Road, AlphaBay, and Hansa. The dark web isn’t just one sketchy marketplace hiding in a corner of the internet; it’s more like a messy, unregulated community with everything from freedom fighters to full-blown cybercriminals. With the onion browser, you can access ordinary HTTPS websites on the web. This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. You only need to upload your PGP key or let the platform create one.