The archived page is then assigned a unique URL, which can be used to access the snapshot at any time, independent of the original web page’s status. This feature is especially useful for preserving evidence of web content that may be legally or historically significant. The Comic Book Library is a digital archive dedicated to the preservation and dissemination of comic books, graphic novels, and related paraphernalia. This repository serves as a comprehensive resource for enthusiasts, scholars, and the general public interested in the rich history and diverse culture of comic books.
Use A Secondary Non-admin Account
The .onion version helps users in restrictive regions or those looking for more privacy. Torch is one of the oldest dark web search engines, having served the darknet community for years. It boasts a vast archive of over 400,000 pages, providing comprehensive coverage of .onion sites, including forums, blogs, and marketplaces. The forum specializes in a variety of illegal activities, including the sale of leaked data, hacking tools, and fraudulent services. Despite its focus on illicit content, Nulled has a large and active user base.
- I think it’s safe to say that these are unsanctioned exploits, all the more reason to boast them on the dark web.
- The blog contains tons of useful guides about how you can avoid online surveillance.
- But those tiers don’t have much influence on dark web prices, which are largely governed by account balance.
- The “surface web,” on the other hand, is the publicly available part of the internet that search engines index.
- Ahmia promotes transparency by being open-source and allowing contributions.
MICROSOFT SECURITY TOOLS

Though not specifically a .onion service, Keybase integrates well with privacy-focused ecosystems like Tor. It offers features like encrypted communication for chats and file sharing, making it popular with privacy-conscious individuals. The CIA (Central Intelligence Agency) provides a .onion version of its website, enabling individuals to bypass restrictions to access its content from anywhere. This platform allows visitors to anonymously explore the World Factbook, submit information, apply for jobs, and perform any other actions available on the CIA’s main site.
Enjoy More Secure Browsing With A VPN
Cyble’s platforms, such as Cyble Vision, monitor the dark web for emerging threats, providing real-time insights to protect organizations from cybercrime. By leveraging such tools, businesses and governments can protect their data and communities from cyber actors. Exploit.in, founded in 2005, is another prominent Russian hacker forum. Operating on both the dark web and the surface web, Exploit.in serves as a hub for malicious actors seeking to buy and sell exploits, malware, and stolen data. The forum is notorious for its role in facilitating unauthorized access to networks and distributing malware. The internet we use daily is only a small fraction of the vast digital world hidden beneath the surface web.

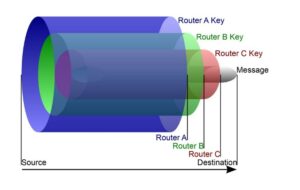
As a result, the recommended browser for accessing the dark web is the Tor (The Onion Router) browser. However, please note this article is for research and educational purposes only. The dark net is full of notorious hackers, scammers, malware, and other viruses. We recommend using NordVPN and a robust antivirus like TotalAV to keep you safe while browsing the dark web. Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity. That’s why we always recommend using a VPN over Tor—even if you feel you have nothing to hide.
Do I Need A VPN If I Use Tor?
AVG Secure VPN encrypts your internet traffic and obscures your IP address every time you use it to go online — dark web or not. With a variety of server locations around the world to choose from, you’ll be able to navigate the web more privately and access the content you want. Bearing in mind all the dangers, if you’re sure you’re willing to accept the risks, all you need to enter the dark web and access onion sites is an internet connection and Tor Browser software.
Encrypted Communication Tools
Exploring the dark web can provide valuable insights and essential privacy, but it requires careful, informed navigation. By selecting trusted search engines, crafting precise search queries, and diligently verifying sites, you can greatly enhance your safety and effectiveness. Remember, good digital habits—such as maintaining anonymity, avoiding risky behavior, and staying vigilant—form the foundation of secure dark web exploration. This makes comprehensive indexing—something Google excels at—almost impossible on the dark web. If you’re curious about how to explore .onion sites safely and effectively, this guide will walk you step-by-step through the process. This solution focuses on identifying stolen data, brand misuse, and potential threats before they can cause significant harm.

This not only protects against financial losses but also reinforces customer trust. This victory against cybercrime dealt a severe blow to the criminal underground, disrupting operations on one of the most prolific dark web platforms. Since the dark web isn’t indexed by standard search engines, sites like Ahmia act as modified directories to help users discover onion sites.
Table Of Contents
- Many people seek it out for privacy and anonymity, as the Tor network and the Hidden Wiki help mask identities and activities from surveillance.
- This lets you check what information it contained at a previous point in time.
- ZeroBin has a cool autodestruct feature that makes the message go kaboom (not literally) after the recipient reads it.
- Learn to fetch data, analyze content, and generate reports automatically.
- Dark web credit cards are often sold on online marketplaces, which can be accessed through specialized browsers like Tor.
- I found it especially useful for testing new services without risking my main email address, though messages expire after 24 hours.
Card data on the dark web is a valuable commodity, and it’s often sold on specialized marketplaces known as Card Shops. These platforms are hubs for cybercriminals to buy and sell compromised payment card details. These platforms serve as hubs for cybercriminals to easily buy and sell compromised payment card details, including credit card numbers, CVV codes, expiry dates, and cardholder information. The dark web remains a largely unregulated and unmonitored part of our digital world.

The software requires two-factor authentication to receive what’s been uploaded by the whistleblower and allows two-way communication between the anonymous contact and the media outlet. Although profiting from pirated copyrighted material is unethical and illegal, there are some exceptions to using copyrighted material, such as a “private study” provision under UK law. In addition to web hosting, Impreza Hosting offers Virtual Private Server (VPS) hosting, domain registration, and specialized hosting solutions tailored to the needs of its clients. Users of Archive Today can archive web pages by simply entering the URL into the service’s web interface.
Some vendors offer a “complete package” known as “Fullz”, which includes full personal details as well as financial details like bank account information or social security numbers. If your PayPal account or credit card details end up on the dark web, it’s essential to act quickly to minimize potential damage. Full or partial credit card details are commonly sold on the dark web, including BIN numbers, credit card numbers, expiration dates, and CVV numbers.
As such, they are normally under intense scrutiny from law enforcement and security professionals alike. To minimize the risk of payment data exposure, only shop from reputable retailers, use digital payment methods or one-time private cards, and protect your accounts with two-factor authentication. The forum is available in English and accessible via the regular web, making it more user-friendly than many similar platforms. Beyond simply exchanging leaked information, LeakBase also operates as a mini-market where users buy and sell compromised data.
In a similar study earlier this year, we noted an average price of 3.13 cents per dollar in the account. So unlike credit cards, prices for PayPal accounts and transfers have gone up during the pandemic by 293 percent. Due to limited data on credit cards from other countries, we were unable to adequately compare prices for credit cards from different places. Safe browsing on the Hidden Wiki requires a combination of technical precautions and behavioral discipline. Always access the Hidden Wiki through the official Tor Browser, never via a standard browser. Disable JavaScript and other potentially risky browser features unless necessary, as they can be exploited to reveal your identity.
Cryptocurrencies weren’t so popular among the general public until recently. However, dark web users have relied on Bitcoin transactions for over a decade, as they allow people to make payments while staying completely anonymous. And Hidden Wallet is one of your best options if you’re looking for a Bitcoin wallet for use on the dark web. There’s much more to learn about the dark web, but here, we’ll focus on listing the best .onion sites you won’t find on Google.
You should never use your personal information on the dark web anywhere else in your life. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. Blockchain even has an HTTPS security certificate for even better protection. Talking about copycats and potential risks, due to its high risk and low signal-to-noise ratio for legitimate content, we advise beginners and privacy-conscious users to avoid The Hidden Wiki. If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites. Since then, BidenCash has continued to operate using the “dumping” method.