You can access most of the Deep Web using the same browser you use for the Surface Web. Additional steps depend on what type of Deep Web content you’re looking for. The use of the dark web usually means that you are attempting to engage in activity that you could not otherwise carry out in the public eye.
Take a closer look at the differences between the two, and use Norton 360, with built-in VPN and AI-scam technology, to encrypt the data you send and receive online and help protect against scams. Accessing content on the deep web is relatively safe, and most internet users do it all the time. Logging into Gmail or LinkedIn, or signing in to the Wall Street Journal are just a few examples of accessing data on a deep web site. Crawling is the process by which search engines scour the internet for new content and websites.

Other Privacy Tools And Services
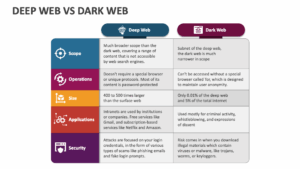
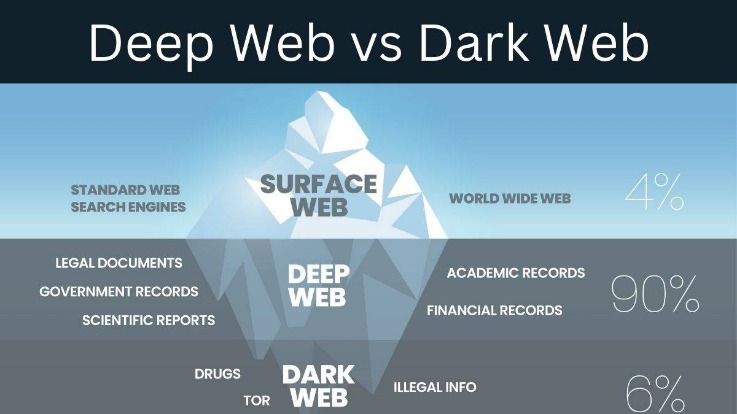
The Internet is sizable with millions of web pages, databases, and servers all run 24 hours a day. But the so-called “visible” Internet (aka surface web or open web) — sites that can be found using search engines like Google and Yahoo — is just the tip of the iceberg. Tor also lets people access so-called hidden services — underground Web sites for which the dark Web is notorious. Instead of seeing domains that end in .com or .org, these hidden sites end in .onion.
What Is The Deep Web?
Lastly, but certainly not least, if you encounter any illegal or harmful content while exploring the Deep Web, it’s essential to report it to the appropriate authorities. This contributes to making the online environment safer for everyone and helps in cracking down on illicit activities. One of the golden rules of navigating the Deep Web safely is to refrain from sharing personal information. This includes not using your real name, email address, or any identifiable details when registering or participating in discussions. By maintaining a high level of anonymity, you can safeguard your online identity effectively.
- Many services that are allegedly offered on the dark web are scams.
- It’s important to arm yourself with a good VPN (Virtual Private Network) when you want to enter the dark web to protect your privacy and anonymity.
- For example, the URL of Silk Road is rather unintelligible and may look something like “gan4arvj452janndj4a76.onion”.
- Most dark web pages are onion websites, which are not accessible by all browsers but only to a select few.
- The deep web is used to access a wide variety of different web pages and online information in a way that retains its privacy.
Best Dark Web Sites: Unseen Onion And Tor Links
Join 15,000+ developers who receive weekly updates on exclusive discounts, special offers, and verified promotions. You’re free to read and post such content on the dark web, but know this – visiting the dark web is a bit like going to a nightclub or a bar with a very bad reputation. You may end up being robbed, accidentally seeing things you didn’t wish to see, and in case of a raid, just being there can get you in trouble.
The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. Onion links have no regular domain names registered under the domain name registry. Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser.
You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. Platforms like SAGA by Munit.io deliver these insights in real time, so security teams can move from reactive to proactive defense. By identifying early-stage threat coordination or mentions of internal assets, organizations can take preventative action before attacks escalate.
That’s not to say that the entire deep web consists of these difficult-to-find websites. The deep web fulfills a range of needs, from allowing people to host and access digital content away from the prying eyes of authoritarian governments, to facilitating a range of illegal activities. Whenever you’re on a dark web site, avoid dropping any personal information. Create anonymous profiles for any website you register with on the dark web.
And if someone tries to access the deep web without proper authorization, it would be termed as hacking, which is again illegal. From apps to advertisers, many services track your real-time location—even when you’re not a… Avoid phishing links, unknown files, and suspicious login portals to prevent security risks.
Access To Specialized Content:

Both of these are excellent utilities you can try without second thoughts. There are many, but my personal favorite is ProtonVPN (free version available). If you’re still up for looking at the dark side of the internet for reasons best known to you, here are a “few” things to take note of. People use it to share information when their local governments act hostile or snoop extensively.
- Its goal is to offer anonymous access to the content without being censored, no matter where you live.
- Despite the deep web’s bad reputation and terrible PR, it’s not inherently more dangerous than the surface web.
- Deep web sites may be concealed behind passwords or other security walls, while others simply tell search engines to not “crawl” them.
- You can either sell or buy goods on the dark web, but both present difficulties.
- Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together.
Resources
So yes, the onion network and the deep web are both legal, it’s only the dark web which is illegal and may cause problems for you. You also need to know that more than half the sites and sellers on the Dark web can’t be trusted, and are just scammers. That’s so because it’s already an illegal arena, so you can’t exactly go to the authorities about it.
Fee-for-Service Sites

The absence of regulation on the deep web can result in the proliferation of harmful content, including but not limited to extremist propaganda and misinformation. Often, what you can’t find in a search engine, you can find in various government and open access journals that you can search on Google. One example is USA.gov, which houses all files connected to the U.S. government. You just need to be online to use its web pages, like webmail, social media platforms, or a payment gateway. Many times, it requires two-factor authentication with a one-time password. The Deep Web raises important questions about privacy, security, and ethics.
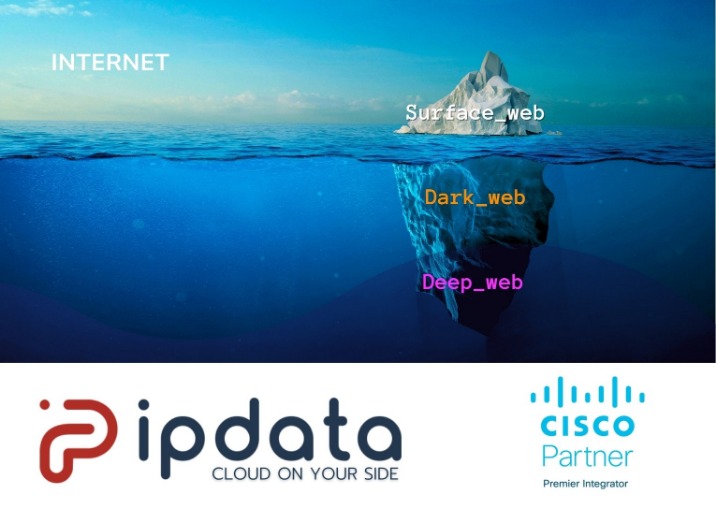
The reputation of the dark web has often been linked to criminal intent or illegal content, and “trading” sites where users can purchase illicit goods or services. Locating surface web websites is possible because search engines can index the web via visible links (a process called “crawling” due to the search engine traveling the web like a spider). You can find illegal goods and activities of all kinds through the dark Web. That includes illicit drugs, child pornography, stolen credit card numbers, human trafficking, weapons, exotic animals, copyrighted media and anything else you can think of.
Privacy Protection:
It is one of the most reliable options for streaming or downloading content. Its ultra-fast and secure servers provide smooth browsing on deep webs. If the antivirus confirms that a file poses any danger to your device, it warns you. High-quality antivirus programs regularly scan your device to ensure malware, spyware, Trojan horses, or other malicious software haven’t compromised it. For a web page to be on the surface of the web, such as on Google search engine result pages, a web crawler must first crawl and index it. That means you decide whether you want any search engine bot to crawl your webpage.
Secure Communication:
Many sites use this file to intentionally exclude sensitive or irrelevant content from search engine results. As long as there’s a demand for the ability to privately browse the internet and, more importantly, host websites anonymously, the deep web will exist. Due to its decentralized structure, there is no real way to “shut down” the deep net, just like you can’t really shut down the regular internet. You can also use security tools with AI-powered scam detection capabilities to identify and block suspicious links and websites in real-time when browsing the dark web.