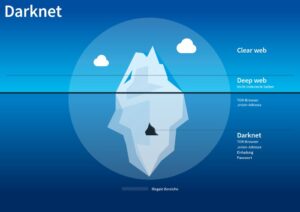
The use of onion addresses and Tor networks further enhances user privacy, making it nearly impossible for...
store
Furthermore, regular cybersecurity risk assessments would have identified weak authentication systems, allowing the firm to implement stronger...