He recommends verifying market employees carefully, and to weed out law enforcement infiltration through barium meal tests....
darknet
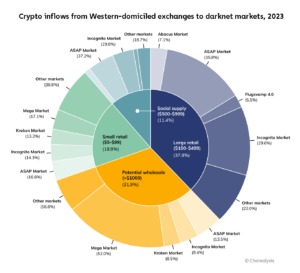
However, the trade in entertainment accounts with less immediately obvious value for identity thieves continues to flourish....
Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address...
This guide outlines different ways of safely accessing dark web stores and the list of reliable dark...
Each listing is reviewed and rated by verified buyers, with vendors offering lab testing results and usage...
A lot of vendors from all over the world are registered here, offering an extensive range of...
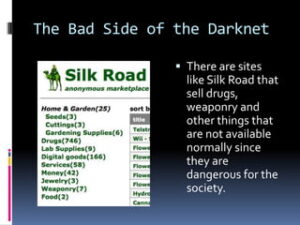
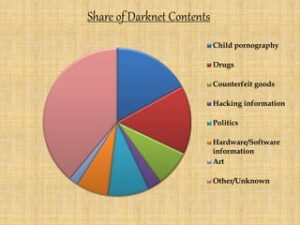
Unfortunately, the dark web hosts not only explicit but also deeply illegal and disturbing content. It’s also...
He says most of the sites on the regular internet, which the Senate report focused on, are...
A new, technically advanced market called White House has also been launched, gaining 10,000 listings, 100,000 users...
Market URLs change rapidly nowadays on the dark web, to escape malicious hacking by blackmailers. This exposes...