Avoid using payment methods that can easily expose your identity. Today, many organizations exist that are created only to handle these reports anonymously and effectively. They know how to process the information and get it to the correct law enforcement agencies internationally. We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch.
This is why I strongly advise anyone visiting the dark web to exercise the greatest of caution during their dark online travels. Check out my article for more information about the dark web and how to access it while staying safe. One way to stay safe is to use a VPN while accessing the dark web, so be sure to check out my article on the best VPNs for the dark web.
Is Using Tor Safe?
In such cases, the “Configure Connection” option becomes necessary. Clicking this button will lead to a series of configuration options designed to help users bypass censorship or accommodate specific network setups. All v3 .onion addresses (the current standard) are 56 characters long and end with “d” to denote the URL version in use.
What’s The Difference Between Tor And VPN?

These services utilize unique web addresses ending with the .onion top-level domain, signifying that they are accessible only through the Tor network. Unlike conventional web addresses that rely on the Domain Name System (DNS) to translate human-readable names into numerical IP addresses, .onion addresses have a distinct structure and function. A standard v3 .onion address consists of a 56-character alphanumeric string followed by “.onion”. These seemingly random strings are actually derived from the service’s public cryptographic key, which provides a form of inherent, albeit limited, self-authentication. This cryptographic basis ensures that the address is directly linked to the service’s identity within the Tor network.
Step 4: Adjust Security Settings
Clicking on random onion links is quite risky and isn’t recommended. A random dark web link can lead you to malicious software, phishing sites, and illegal content. Both DuckDuckGo and Ahmia are safe choices for finding Tor Browser links without being tracked. Any onion websites you visit from these search engines is another story.
Law Enforcement Interventions

Ratings are easily manipulated, and even sellers with long track records have been known to suddenly disappear with their customers’ crypto-coins, only to set up shop later under a different alias. All this activity, this vision of a bustling marketplace, might make you think that navigating the dark web is easy. The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others. The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below.
Do I Need A VPN To Access The Dark Web Using Tor?
It uses TrustedServer technology on the entire server network to wipe out your data after every session. While people and organizations do host legitimate and useful sites on the dark web, it’s still best to tread cautiously. Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too.

Government Monitoring
The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor. The dark web is a very popular platform for journalists, political bloggers and political news publishers, and in particular, those living in countries where censorship shields most of the internet. The users of the dark web are typically aiming to block governments from snooping on them.
Although the social application is known for collecting data on its platform, it does not like sharing the information with others. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security. We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal. The Tor network began as an anonymous communications channel, and it still serves a valuable purpose in helping people communicate in environments that are hostile to free speech. “A lot of people use it in countries where there’s eavesdropping or where internet access is criminalized,” Tiquet said.
Originating Traffic
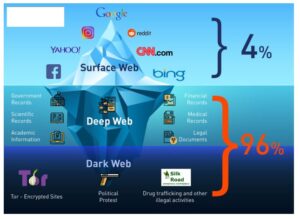
Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs. The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content. It can also reside in web archives, non-HTML pages, and so forth. That means that only 0.024% of all the known pages are findable in Google’s search engine.
Darknet Markets
Tor (network), a free software platform designed to protect users’ identities while they are browsing the Internet and exchanging messages. “If the site invests in setting up a ‘native’ Tor onion-address for their website, then people who use the Tor browser to access that address never step outside the protection of the Tor cloud,” Muffett says. “The Tor network is another network which sits on top of the TCP/IP internet, stitching the participating computers together into a wholly new network ‘space’, not IPv4, not IPv6, but ‘Onion Space’.”
- For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question.
- Nevertheless, most people on the internet do not need to communicate or venture into the dark web.
- Some hospitals even have classified medical records you can’t access just like that.
- Only the first and last nodes can reveal the identity of the sender and the content of the message.
- You’ll find articles on a wide range of topics, such as history, science, and culture — and that’s just scratching the surface.
Here are some of the popular ones, exclusively hosted in the darknet. Web search in late 90x, total fun – that required luck and skill. Search algorithms back then used to be based on exact words matching and presented based on resource popularity and number of cross-references. Btw today’s search engine provides you with information that the algorithm considers being your intend (adjusted to probability), and there is far more complexity involved.
As conventional browsers cannot display .onion addresses without considerable modifications, Tor clients are also encouraged to use the Tor Browser, a version of Firefox. Tor claims that it is the best browser for its network for ensuring the greatest possible anonymity. A more recent and potentially more reliable method for discovering onion services is through the “Onion-Location” feature. This is a non-standard HTTP header that website administrators can implement on their regular (surface web) websites to advertise if they also have an onion service counterpart. If a user visits a website that has implemented Onion-Location using Tor Browser, a purple suggestion pill will appear in the URL bar, displaying “.onion available”. Clicking on this prompt will automatically reload the website and redirect the user to its onion counterpart, providing a more secure and private connection through the Tor network.
This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk. Even after Silk Road went down, dark web marketplaces haven’t slowed down. Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement. Later, in 2013, Silk Road caught the attention of law enforcement and policymakers like US Senator Charles Schumer, who publicly called for a federal crackdown.