It is considered very secure thanks to strict user validations and transparent payment and vendor review procedures. Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web. Quality and validity of the data it provides justify its higher cost over other marketplaces. The platform’s popularity continues to grow, attracting both new and returning customers. STYX Market focuses specifically on financial fraud, making it a go-to destination for cybercriminals engaged in this activity. Accessing darknet requires using Tor Browser, a special web browser that routes your internet traffic through a global network of relays managed by volunteers.
Trump Media’s $64 Billion Crypto Push: What It Means For CRO, Politics, And The Future Of Crypto Adoption

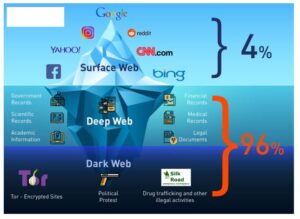
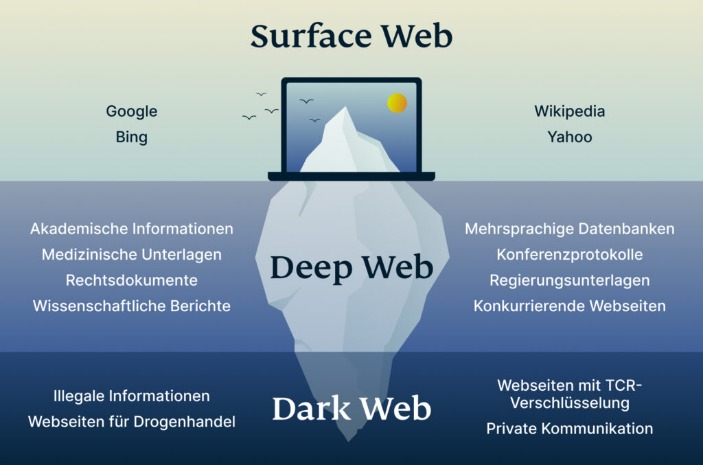
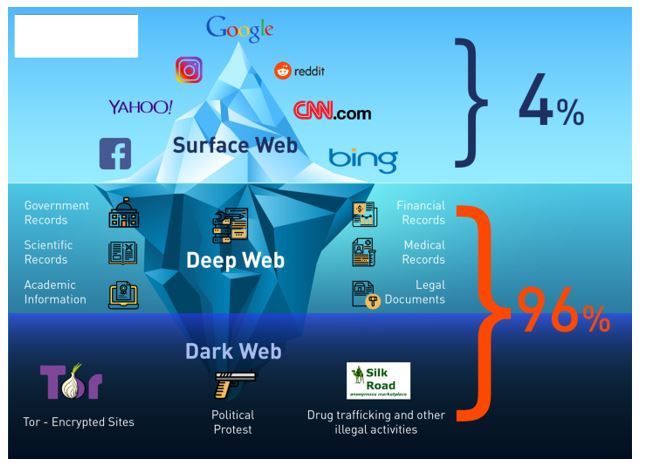
Finally, the article will highlight the escalating risks tied to financial crimes and data breaches, both of which have become alarmingly common in recent years. As ransomware attacks surge and personal data is increasingly commodified, the Dark Web stands out as a primary facilitator of cybercrime operations. By reviewing these complex dynamics, we aim to equip readers with a comprehensive understanding of the threats posed by Dark Web marketplaces—and the strategies needed to combat them. The Dark Web stands as one of the most enigmatic regions of the internet, offering covert access to illicit marketplaces that operate outside traditional law enforcement oversight. Despite aggressive crackdowns, these hidden markets continue to thrive and adapt, providing an ever-expanding range of illegal goods and services. Understanding the driving forces behind their growth—alongside the mechanics of how they function—is crucial for both cybersecurity professionals and policymakers tasked with mitigating emerging threats.
North Korea Hacks Crypto: More Targets, Lower Gains
Understanding the nuances of the dark market 2024 becomes essential for anyone interested in cybersecurity, digital privacy, and global economics. While accessing Darknet Markets themselves is typically not against the law in most places, engaging with illicit goods within them is generally considered a crime. On the other hand, some people might visit Darknet Markets for lawful purposes such as research, journalistic work, or simply to explore online communities. It’s essential to know the local laws regarding online activities, and be cautious when using these platforms to avoid any potential issues.
One of the biggest winners is Axie Infinity — a Pokémon-inspired game where players collect Axies (NFTs of digital pets), breed and battle them against other players to earn Smooth Love Potion (SLP) — the in-game reward token. This game was extremely popular in developing countries like The Philippines, due to the level of income they could earn. Players in the Philippines can check the price of SLP to PHP today directly on CoinMarketCap.

CISA Strengthens Software Procurement Security With New Tool
During this initial stage of money laundering, criminals can use the profits obtained through illegal activity to purchase cryptocurrencies. Related to phishing, impersonation scams involve criminals posing as well-known individuals or organizations to deceive victims into sending funds or revealing sensitive information. Account compromises can expose users’ pseudonymous identities, while crypto wallet theft remains a prevalent threat when hackers intercept private keys. De-anonymization of both buyers and sellers can happen through advanced tracking techniques, such as malicious software implants or poor operational security practices.
Easy Steps To Access Dark Web On Your Phone Safely In 2024
The markets often share materials related to child exploitation, pornography, and non-consensual recordings, all of which are serious crimes that inflict lasting harm on real-life victims. Understandably, as in the case with most illicit trade markets, you don’t even need to verify your email Awazon. Now that you understand what the dark web is all about, you might wonder why other people do things on it. Darknet marketplaces like to exist on the dark web because it offers a service that the regular internet, or more accurately, the “surface web,” does not. Despite these efforts, dark web operators rebuild quickly, often with better security and decentralized tools.
Government Shared Services
While Bitcoin is the most well-known cryptocurrency, there are several other digital currencies that are commonly used on the dark web. Each of these cryptocurrencies offers its own unique features and benefits, but they all share the common trait of providing a level of anonymity and privacy that is attractive to those operating on the dark web. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data. The report also revealed that despite a likely record year for overall crypto crime revenue, inflows to darknet markets and fraud shops declined in 2024.
- Buyers simultaneously active on multiple markets also play the role of connectors in the ecosystem.
- However, enforcement inconsistencies highlight the ongoing struggle between financial privacy and regulatory oversight in combating cryptocurrency-enabled money laundering.
- The use of blockchain intelligence tools to monitor crypto services that offer privacy coins helps law enforcement and regulators to identify on-ramps and off-ramps involving these protocols.
- Striking a balance between regulatory control, user privacy, and technological progress is essential for a secure, inclusive digital financial future.
- And in a world where almost everything we do is online, taking your digital privacy seriously is more important than ever.
- In total, nearly USD 4 billion was stolen in 2022 through the main types of crypto theft studied by TRM Labs.
It contains a good selection of product listings that range over 35,000 items. It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security. Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services. The shop accepts payment through Bitcoin and Monero, while some vendors accept the coins. The vendors aren’t required to register or apply for a vendor account while using this platform. It ensures the buyer’s identity is kept hidden and accepts payments through cryptocurrencies, including Bitcoin, Litecoin, Ethereum, and Monero.
Is Claude Safe And Secure In 2025?
These addresses were linked to perpetrators of romance scams, investment scams, impersonation scams and others as neutral platforms enabling payment by victims. Until its creator shut it down in 2023, Monkey Drainer was one of the latest major drainware tools targeting the crypto industry en masse. The malicious contract required users only to approve and sign transactions, making it simpler than many traditional attack methods. Most of the stolen cryptocurrency from Monkey Drainer was laundered through Tornado Cash. In some cases the fraudsters used intermediary wallets before attempting to cash out stolen funds at three centralized exchanges.
Espionage activities can involve the covert transfer of funds to support intelligence gathering or other covert operations. Cryptocurrencies can provide a discreet and secure means of transferring funds, making them an attractive option for state or non-state actors engaged in espionage. Most major BPHS entities require manual setup, including, for example, a mass-scan of a network.
- Additionally, the United States urges the international community to effectively implement international standards on AML/CFT in the virtual currency area, particularly regarding virtual currency exchanges.
- Although dark-web marketplaces utilize technologies like Tor and I2P to enhance anonymity, these methods are not foolproof.
- In response, governments are enhancing blockchain surveillance and enforcing stricter regulations to combat crypto-enabled cybercrime.
- The best dark web sites provide access to educational materials, host secure services, or bypass government censorship.
Crypto did not introduce these criminal forms; nor has it (yet) come to dominate them. The year saw as much as USD 2 trillion worth of cryptocurrency assets wiped out from investors’ balance sheets, according to World Economic Forum estimates. Yet the fall in crypto’s value does not appear to have dissuaded criminals from using and exploiting crypto.
Q: Which Cryptocurrencies Are Commonly Used On The Dark Web?
This for a large part will be driven by the maturing of transaction monitoring and blockchain analysis tools like those supplied by Crystal Blockchain, Chainalysis and ScoreChain. These tools support law enforcement agencies and financial institutions in detection, investigation, and the de-anonymising process of suspicious transactions. Compared to Bitcoin, Monero so far has proven to be much more complex to track. Parasite VASPs rely on the architecture of a larger exchange to provide digital assets trading services to users, often without the knowledge or consent of the host exchange.
They help establish trust between buyers and sellers by holding payments until both parties confirm the deal’s completion. In tandem with escrow, robust feedback mechanisms allow users to review sellers’ reliability. These rating systems shape market reputations and encourage fair dealing, at least within the confines of illicit trade.