Finally, the growing demand for stolen data used for illegal activities such as identity theft, fraud and phishing is helping to strengthen the market. The reliable relationship between vendors and customers was mirrored in customer feedback on vendor reliability which often manifested in users declaring themselves as repeat customers (T4). The reported issues about vendors not sending the product (T2) confirm that the conflicts that challenge the vendor-customer relationship are manifested in the financial victimisation of customers (Bergeron et al., 2022b). These results suggest that risk awareness campaigns should focus on the risks of payment transactions and product delivery (Bradley & Stringhini, 2019; Jardine, 2021).
Model Estimation
To tackle these obstacles, law enforcement agencies have developed various strategies. They employ advanced technology to monitor darknet activities, focusing on identifying patterns and gathering evidence against criminals. These hidden corners of the internet have become hotspots for the online drug trade, providing access to a wide range of illicit substances that are just a few clicks away.
At scip AG, we offer darknet monitoring services to inform companies about potential data leaks and the misuse of sensitive information at an early stage. Through the targeted use of our proprietary AI bots, we are able to infiltrate relevant darknet markets and perform real-time speech analysis. This enables us to identify transactions and actors that are of importance to our clients. As soon as a suspicious case is identified, our specialized darknet monitoring team is informed.
Crypto Crime Value Likely Hit A High Of $56 Billion In 2024, Says Report
Therefore, given the nature of anonymity and privacy of the dark web, several stores keep on emerging in the dark despite a continuous crackdown on several others. We understand the curiosity to venture into the dark web, but you also need to understand that it’s never safe to venture into this portion of the internet without fully understanding what it entails. Overall, dark-web marketplaces inherently involve substantial risk, and users must thoroughly understand these threats. Anyone considering engaging with these platforms must carefully evaluate potential consequences, exercise stringent security practices, and remain vigilant to minimize exposure to these significant hazards. Dark-web marketplaces often attract attention due to their association with illicit activities; however, these platforms also serve legitimate purposes that align closely with principles of online privacy and freedom of information.

This includes regularly updating software, using strong passwords, and enabling two-factor authentication. Darknet markets also offer counterfeit goods that mimic high-end brands at a fraction of the price. Whether you’re after luxury handbags, designer clothing, or even electronics, there’s no shortage of knockoffs available for purchase. It’s like having access to an underground mall where you can find anything your heart desires. The information-stealing malware package that Genesis Market used to exploit victims included a hidden Chromium-based browser plugin, made to look like a Google Drive plugin, which captured credentials stored in victims’ browsers. Fentanyl and fentanyl-laced drugs also arrive in the United States through Latin America based cartels.
Essential Security Tips For Using Dark-Web Marketplaces
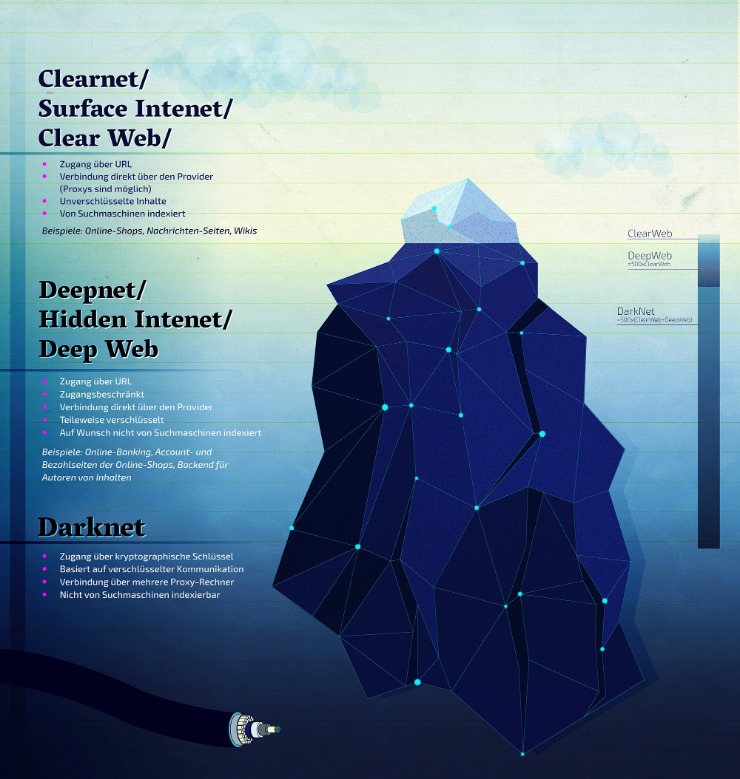
The amount of information on the web is growing, with most people only accessing content on the surface of the web via traditional search engines. The deep web, on the other hand, is a huge collection of web pages, mostly from database-driven websites, which make up a large part of the entire web. A hidden area of the internet, the darknet, is part of the deep web and is only accessible via specialized software such as the Tor browser, I2P or Freenet. Dark markets provide a one-stop-shop for cybercriminals, offering a wide range of services such as hacking tools, stolen data, ransomware, and Distributed-Denial-of-Service (DDoS) attacks for hire. This increases the accessibility and sophistication of cyber threats, with far-reaching consequences for businesses. To secure against these risks, organizations invest in robust cybersecurity strategies, conduct regular security assessments, and educate employees to recognize and mitigate threats.
An example of intervening at this stage was Operation Bayonet, where Dutch law enforcement agencies took over an entire darknet market and gained direct access to user data. The kind of operation which damages trust among the actors by actual data or financial loss of the users is more effective than simply removing a market from the darknet (Bradley & Stringhini, 2019). The third stage of the crime script is the actual market use when vendors advertise themselves and their products while customers select and order what they are looking for (Jardine, 2021). Notifying individuals that they have been observed engaging in darknet market activities could deter them and other users from future use of the platform by showcasing the intelligence-gathering power of law enforcement.

What Happens To Stolen Data
- To stop the marketplaces is not a walk in the park as it takes immense effort from authorities like the FBI and international law enforcement.
- This attention can be too much for some markets, which will voluntarily close rather than remain an obvious law enforcement target for too long.
- Apart from the dark web markets that are operating online today, some raided platforms influenced many markets.
- The story of dark web marketplaces kicks off with Silk Road, launched in 2011.
- These tools scan dark web forums and marketplaces for any signs of your compromised credentials.
From opioids to stimulants, these markets cater to every desire, allowing users to purchase drugs without leaving the comfort of their own homes. In conclusion, the rise of darknet markets has had a profound impact on both our society and economy. As individuals seeking belonging in today’s interconnected world, it’s crucial that we remain vigilant against this ever-present threat and work together with law enforcement agencies to ensure a safer digital landscape for all.
Experience The World’s Most Advanced Cybersecurity Platform
An analysis by the Federal Office for Cybersecurity (BACS) revealed that around 65,000 of the 1.3 million data records published were relevant to the Federal Administration. Around 9,000 of these documents could be attributed to the Federal Administration, with around 14 percent containing sensitive content such as personal data, technical information, classified data and passwords. The hacker group Play, which was responsible for the attack, had captured 900 gigabytes of data. As Xplain did not respond to the ransom demand, the data was published on the darknet. If you think the Dark web marketplaces are just online shops, you’re wrong — these sites are the actual weapon stores for criminals. They provide criminals with access to everything they need, from launching attacks to stealing data, etc.
Topics And Products Sold
Eventually, the system collapses, and most people lose their entire investment. The UNODC (United Nations Office on Drugs and Crime) maintains that almost all firearms are originally manufactured through legal means. Both Blacksprut and Mega have also sent funds to deposit addresses on this exchange used previously by Hydra, but none as much as OMG. We can see this on the chart below, which shows the total amount sent by each market to shared deposit addresses. It has a bidding feature, with new batches of stolen data being frequently added. Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2024.
While you could find all sorts of products on Silk Road, drug sales quickly became prevalent because of the profits it raked in. In fact, by 2013, a Guardian article revealed that about 70% of listings were drug-related. Too-good-to-be-true investment offers are another classic scam on the dark web. Early participants may see some profit, but that money usually comes from new victims, not actual earnings.
When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements. It scans darknet marketplaces and hacker forums to alert you instantly if anything shows up. This way, you can catch any leaks and stop them before they cause bigger problems. Once many users begin to rely on the site and store funds in escrow, the operators disappear, taking all the money with them and leaving their customers and clients with nothing. Unfortunately, the dark web hosts not only explicit but also deeply illegal and disturbing content.
New Shamos Malware On Mac: Beware Of ClickFix Attacks
On one hand, it offers privacy for whistleblowers, journalists, and citizens in oppressive countries. On the other hand, it’s notorious for enabling illegal activity, including drug sales, weapons trafficking, counterfeit ID trading, hacking services, and the exchange of stolen personal data. Monero and Bitcoin are two of the most commonly used digital currencies on the dark web markets.
In addition, the trustor’s uncertainty is reduced since the trustor can control the trustee’s past behaviour. Buyers can trust sellers’ claims due to the emphasis sellers place on maintaining their reputation 27,44,46–49. Consequently, the establishment of reputation systems becomes imperative to address issues of distrust and malfeasance in markets 50–53.
Accordingly, long-term participation in the market becomes a signal of the concept of the’shadow of the future’, suggesting that expected future interactions influence present behaviour. Similarly, the lifespan of criminal actors on online carding forums, particularly in the form of’long-term participation in the market,’ has been identified as an indicator of trust 29, 144. Prior research also identified the length of time vendors are active on the sites as a signal of trust 33, showing that seniority is significantly and positively correlated with criminal opportunity. This suggests that longer engagement may improve criminal performance, which indicates reliability. It is, therefore, reasonable to hypothesise that the longer sellers have been in the market, the lower the probability or number of fraud cases. Darknet markets commonly display the seller’s registration date, as Alphabay market proves (S1 Fig).



