
This forum is actually attached to the Topsells market and is also used to discuss problems/reviews about orders. However, in terms of registered users and active threads about carding it’s definitely one of the best. STYX Market focuses specifically on financial fraud, making it a go-to destination for cybercriminals engaged in this activity.
- Thefact that credit card (CC) information is already stored on thedevice and added to the wallet immediately triggered the attention ofcybercriminals.
- It’s much more likely that they will have purchased them from another cybercriminal who perhaps uses a card skimmer or banking trojan to harvest payment credentials.
- Some ofthe e-SIM offerings have been observed to originate from Hong Kong,Japan, and the United States.
- Marketplaces frequently employ an escrow system, temporarily holding cryptocurrency payments until buyers confirm that the purchased credit card data is valid and functional.
- A skimmer usually refers to a small, physical device that allows criminals to obtain information from a card’s magnetic stripe when it’s inserted into or swiped on a payment machine.
- They are on top of the latest TTPs and monitor rising threat groups, malwares and trends.
Where Is A Card Number On A Credit Card: A Simple Guide
Certain regions and countries offer more lenient regulations or limited law enforcement capabilities, providing safe havens for cybercriminals. Forums often have policies that reflect these geopolitical realities, such as not sharing data about certain nations. Dark web forums use advanced encryption techniques to secure communications between users. This ensures that messages, transactions, and data exchanges remain confidential and protected from interception. Founded in 2005, Exploit is a leading Russian hacker forum operating on both TOR and the surface web. It connects cybercriminals with collaborators for hacking, fraud, and RaaS activities.
Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. It was the first big site where people could anonymously buy drugs using Bitcoin, and it gained a lot of attention, until it was shut down by the FBI in 2013. Others suggest that the future of carding will move to other platforms, like Telegram – although not all users trust the instant messaging service. One prominent dark web carding market that had been active for almost a decade has also recently shut down – in this case, the operators claimed they were retiring, having made enough money.
Attack-For-Hire Services: The Evolution Of DDoS
Breachsense monitors the dark web, Telegram channels, hacker forums, and paste sites for external threats to your organization. I’ve seen cases where security teams identified compromised card data from their institution appearing on the dark web weeks before they traced the actual breach point. The key is catching this activity before large volumes of card data make it to market. What many don’t realize is that much of this stolen data comes from large-scale breaches rather than individual card skimming. Dark Web credit card fraud is an ongoing problem and is not showing any signs of going away.
Smaller businesses are often targeted because they may lack enterprise-level security infrastructure, making them easier to exploit. Implementing reCAPTCHA v3 or equivalent behavioral-based CAPTCHA helps distinguish bots from humans. The scheme affected 177 victims, compromised 200+ cards, and involved estimated losses exceeding €30,000 (approximately $32K). This shadow economy supports a full-fledged cybercrime supply chain, from data theft to monetization, further complicating mitigation efforts.
Carding Bots
Moreover, Exploit dark web forum features a highly organized structure as well as membership policies that make it attractive to most threat actors. The controlled and professional landscape has led many people to view the forum as the most reliable source. Its popularity can be as a result to the ease of use on it, as the forum features a clean and accessible design with enhanced moderation and a wider scope of the leak topics and sources. But disputing fraudulent charges is a hassle, and carding can have other impacts including negatively affecting your credit score, so it’s important to take steps to protect yourself.
From NFCgate To Track2NFC – The Origin Of Contactless Fraud

I’ve investigated too many breaches where malware jumped from an infected office computer to the payment network. Require multi-factor authentication for high-risk transactions, but it needs to be implemented intelligently. When we spot cards from these BIN ranges appearing in bulk listings, it often indicates a breach somewhere in the payment chain. Pattern recognition through machine learning has revolutionized how we spot compromised cards. Financial institutions and security teams have developed pretty sophisticated detection methods that focus on behavioral patterns. They’ve essentially created a parallel economy with its own reputation systems, escrow services, and even customer support channels.
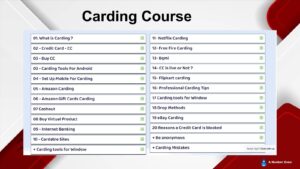
Unveiling The Structure Of Carding Forums
Not only do cybercriminals use it, but Dread has also become a go-to source for cybersecurity professionals to spot emerging threats, track criminal groups, and even understand the trends in the dark web market. To help avoid carding, use reliable anti-malware software to detect malware that could compromise your security, and ensure that your operating system and other software are kept up to date. Additionally, set up credit card notifications to track transactions in real time, helping you catch any unauthorized activity quickly. A dark web carding market named ‘BidenCash’ has released a massive dump of 1,221,551 credit cards to promote their marketplace, allowing anyone to download them for free to conduct financial fraud. Carders use a range of tools and tactics to evade detection while committing fraud. They often rely on proxies and VPNs to hide their true locations, making it harder for e-commerce platforms to flag suspicious activity.
Start Your Protection,
- Cybercriminals want platforms that are there to stay and not taken down by authorities anytime.
- We’re back with another video in our Webz Insider video series on everything web data.
- If you think your site has been carded, look for a spike in small transactions or failed payment attempts, multiple payments from the same IP or device, or increased chargebacks and fraud complaints.
- Each thread on the forum acts like a marketplace, letting users buy the listed products.
- With fraud techniques becoming more sophisticated, businesses must sift through large volumes of data to detect activity that could lead to financial loss or reputational damage.
A positive reputation enhances a member’s credibility, leading to increased privileges, access to exclusive sections, and opportunities for collaboration. Conversely, a negative reputation may result in restricted access or even banning from the forum. By understanding their inner workings and staying one step ahead in the ongoing battle against cybercrime, we can strive to create a safer digital landscape for all. Criminals – sometimes known as “carders” – typically obtain personal data or credit card information by hacking online databases or “skimming” payment cards with malicious software in point-of-sale terminals. WeTheNorth is a Canadian market established in 2021 that also serves international users.
They also underscore the serious consequences faced by criminals—from lengthy prison sentences to substantial financial penalties. Continued international cooperation remains crucial in combating this persistent cybercrime threat. In a notable European effort, Europol spearheaded Operation Neptune in 2020, dismantling a major network specializing in carding and online fraud. The operation targeted criminals across multiple European countries, ultimately leading to 95 arrests and seizure of assets worth over €2 million. Europol’s action dismantled the infrastructure supporting numerous carding operations, drastically reducing illicit activity in the region.
BreachForums is notable for its vast database, with over 15 billion records from 936 datasets. It features sections like Leaks and Stealer Logs and has a unique ranking system. Alongside the obvious sensitive data pertaining to the cards, the dump includes personal information as well, including email addresses, phone numbers, and the address of the card holder.
It also has a premium sales section where cybercriminals can get more exclusive products. However, its most-used feature, as per our research, is the tiered membership system that’s almost similar to BreachForums. A premium user has access to the private Telegram channels that include an exclusive leak channel that’s unavailable to regular members. The fact that it discusses vulnerabilities, legal tools, data leaks, and malware attracts prominent threat actors constantly. Also, it has a strong stance on sharing Russian data, which shows a nuanced approach when it comes to geopolitical sensitivity.
Carders Want Your Credit Card Info
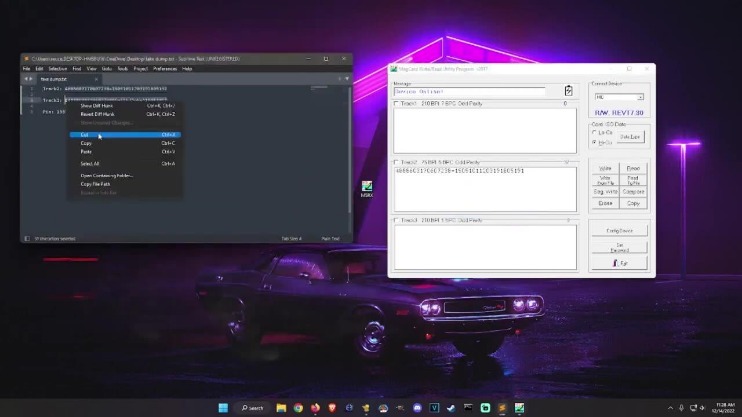
Correlating logs with threat intel sources can help uncover coordinated attacks. 3D Secure adds an extra layer of authentication, often requiring one-time passcodes or biometrics from the cardholder. Security researchers discovered a malicious package on PyPI called disgrasya, which included an automated card-testing script targeting WooCommerce stores. Carding attacks not only cost money but also erode customer trust, damage reputations, and trigger legal consequences if not addressed properly. Protect your devices with strong passwords and encryption to prevent unauthorized access. In the recent weeks, Cyberint has detected a rise in the dark web trade of ‘fullz’, for use in the fraudulent application of disaster loans.
Financial institutions face significant financial burdens, as they must reimburse victims and invest in enhanced security measures. Moreover, the overall trust in online transactions is undermined, hindering the growth of e-commerce. These aren’t just random forums, they’re organized platforms where stolen card data gets packaged and sold as “fullz” (full card details including CVV) or “dumps” (raw magnetic stripe data). Retailers are responsible for keeping the chargeback and payment card-not-present (CNP) levels under control. Payment networks like Visa and Mastercard keep lowering the thresholds for chargeback and CNP credit card fraud and hold merchants accountable with increasing fines and penalties. And payment processors can block all transactions if carding attacks are not handled quickly, which can result in lost revenue to the retailer.



