Depending on how paranoid users are, and what they decide to modify further, within that darknet they’ll have to use another VPN to connect to the person that they want to transact with. So what is a dark web store and why are people who run them so hard to catch? Professor of digital forensics at Edith Cowan University, Craig Valli, explains. Countries differ in how aggressively they monitor Dark Web activity.

This makes sure your messages are encrypted and only readable by the recipient. It’s also about practicing good operational security (OpSec) to help protect yourself and your money. Dark web directories, such as the “Hidden Wiki,” can direct you to authentic. But those directories may not be 100 percent reliable themselves, so take any information with a grain of salt. If you are new about dark web and do not know how to install tor click here. Here i have described how to install tor in step by step process with images and how to stay anonymous.
How To Protect Your Data From The Dark Web
Nevertheless, most people on the internet do not need to communicate or venture into the dark web. Imagine an underground version of your favorite online marketplace, somewhere hidden, exclusive, and often operating outside legal boundaries. It is similar to an online store, except it’s not the type you’ll find with a quick Google search.
Illegal Substances And Weapons
Once you have installed Tor, you can use it to access darknet markets by visiting their onion addresses. Onion addresses are unique URLs that end in “.onion” and can only be accessed through the Tor network. A list of popular darknet markets and their onion addresses can be found on various online forums and websites.
Best Privacy Protection Apps For Ultimate Anonymity And Security
A full explanation of how to make a bitcoin purchase on Localcryptos follows below. The Dark Web is used by cybercriminals to buy and sell illegal goods and services, coordinate attacks, distribute malware and phishing kits, and share other prebuilt exploits. But, perhaps a big surprise to anyone thinking the Dark Web is just for criminal activity, it can also be leveraged for legitimate purposes. Data breaches also present a critical challenge, as stolen credentials allow attackers to infiltrate systems and extract sensitive information, including customer data and trade secrets. These breaches can result in regulatory penalties for failing to comply with frameworks such as GDPR or HIPAA.
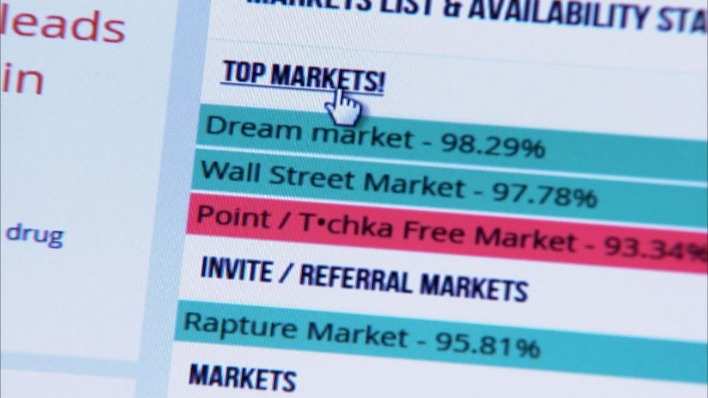
Top Dark Web Marketplaces Of 2025: A Deeper Dive Into Illicit Trade Markets
This unique infrastructure fosters an environment for illegal commerce, posing significant cybersecurity risks for businesses. These markets exist on the Tor network in order to create security and anonymity for both users and darknet providers. Transactions take place via a cryptocurrency like Bitcoin using dark wallets to protect the seller and buyer. The payment is held in escrow by the site operator to discourage scammers.
Additionally, darknet markets are often targeted by law enforcement, so it is important to take steps to protect your privacy and security. Dark web vendors sell detailed guides that teach other scammers how to steal money and commit fraud, often by using products and services that the vendor provides. Common topics for guides and tutorials include hacking, credit card scams, deploying malware and ransomware attacks, social engineering, and digital anonymity.

Choose A Dark Web-compatible Search Engine

Indeed, many people’s first exposure to bitcoin is when they have the need to purchase something off the darknet. For shopping of last resort, you need money of last resort – bitcoin, or possibly monero. Threat intelligence gathered from the Deep and Dark Web is likely to help future threat hunting teams when analyzing telemetry from beyond their own networks, such as the Deep and Dark Web. As stated earlier, neither of these connected content repository networks are illegal to access. Indeed, they must frequently be accessed by cybersecurity organizations conducting threat hunts or defending their networks or those of their clients.
Run Antivirus/Anti-Malware Software
- But in 2013, law enforcement traced Bitcoin activity, monitored DPR’s forum posts, and exploited server vulnerabilities to identify Ross Ulbricht.
- Cybercrime services are more commonly sold through marketplaces, but you can usually find someone offering hacked servers, computer logins, and stolen data on such forums.
- For journalists, intelligence agents, and everyday citizens living in oppressive regimes, the dark web is a critical tool for supporting free speech and open access to news.
- These markets are often used for buying and selling illegal goods and services, such as drugs, weapons, and stolen credit card information.
This incident underscores why dark web monitoring is essential to prevent data breaches for small businesses. A dark web monitoring tool could have detected the compromised credentials early, enabling the firm to reset passwords before the attackers acted. Furthermore, regular cybersecurity risk assessments would have identified weak authentication systems, allowing the firm to implement stronger measures, such as multi-factor authentication. In 2021, a small marketing firm experienced a devastating data breach after employee login credentials were compromised and sold on a dark web marketplace. The stolen credentials allowed attackers to infiltrate the company’s email system, impersonate senior staff, and send fraudulent invoices to clients.
Utilize search engines targeted to index links on the dark web like Torch or Grams__)); But keep in mind these search engines will also show up illegal content. Trust from only reliable sources such as forums or communities talking about darknet activities. Once in a while these forums share links and comments across the different marketplaces. To remain anonymous about your purchases on the dark web, always use cryptocurrency as your mode of payment. If a seller encourages you to opt for other well-known and commonly used payment methods, then the person is likely to be a scammer, and you must not make any deal with them.
A Response To Dolliver’s Evaluating Drug Trafficking On The Tor Network: Silk Road 2, The Sequel
If you’re searching for a reliable dark web marketplace, We The North Market provides secure transactions, encrypted communications, and a low 5% vendor fee. In this guide, we’ll break down the top dark web markets and how to stay safe while using them. We found several thousand vendors selling tens of thousands of stolen data products on 30 darknet markets. These vendors had more than $140 million in revenue over an eight-month period. It’s one of the largest darknet markets that launched in 2022 and trades sensitive financial credential transactions.

Even browsing these sites can put you at risk of malware infections or attract unwanted attention from law enforcement. Brian’s Club has been around since 2014 and remains one of the most well-known credit card shops on the dark web. It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks. Despite multiple takedown efforts by law enforcement and security researchers, Brian’s Club has resurfaced repeatedly and continues to add new stolen credit card data. Abacus Market is one of the newer darknet marketplaces that quickly filled the gap left by AlphaBay’s takedown. It hosts over 40,000 listings and offers everything from illicit goods and substances to hacking tools.



