
However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities. It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it.
Dark Web Markets: Unveiling The Hidden Underworld
Australia has imposed financial sanctions and travel bans on several individuals in relation to illicit cyber activity conducted by ZServers. The group provided bulletproof hosting (BPH) services to the cybercriminals that breached health insurer Medibank Private. “BPH providers are resistant, but not immune, to takedown efforts from law enforcement and requests for cooperation,” AFP says. Don’t ever reveal your true identity on the dark web marketplaces because there’s a high chance of hackers and scammers misusing it. Beware of sharing your financial details on the dark web, as this can result in identity theft and your bank account amount being stolen. This guide outlines different ways of safely accessing dark web stores and the list of reliable dark web marketplaces you can consider visiting in 2025 for research and monitoring purposes.
Cyber-Attacks And Scams
Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime. WeTheNorth is a Canadian market established in 2021 that also serves international users. It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. The story of dark web marketplaces kicks off with Silk Road, launched in 2011.
- Cybercriminals on the dark web marketplace always look for new victims to target them with scams or infect their devices with malware, spyware, or adware.
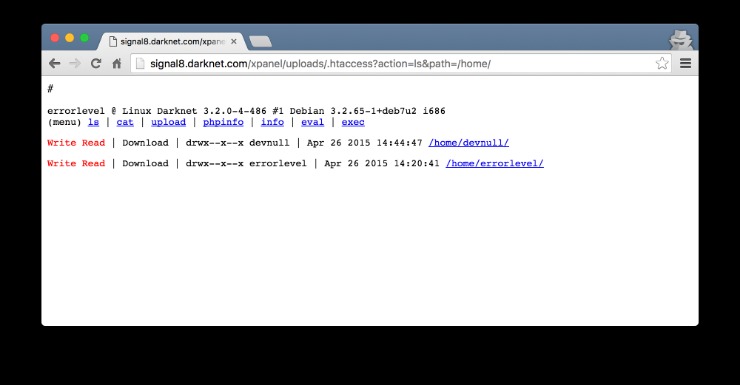
- For example, the URL of Silk Road is rather unintelligible and may look something like “gan4arvj452janndj4a76.onion”.
- While it offers anonymity for legitimate purposes, it is also a haven for cybercriminals.
- The dark web combines encryption, anonymity, and hidden doorways to provide the perfect sanctuary for such illicit activity compared to the usual internet, which is more vulnerable and trackable.
- In this guide, we’ll show you what you need to know about how to access the dark web and how to keep yourself safe while you use it.
- “If the site invests in setting up a ‘native’ Tor onion-address for their website, then people who use the Tor browser to access that address never step outside the protection of the Tor cloud,” Muffett says.
11 Mechanism 2: Platformization
Ensure you download the Tor Browser from the official website to avoid downloading malware, spyware, or other viruses to your device. The easiest way to access Tor is through a special browser known as the Tor Browser. You might want to hide your Tor Browser download using a VPN and your existing browser’s private/incognito mode. This information can be used to target ads and monitor your internet usage.
What Is Tor?
Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though). The best thing is to actually understand how to find the fresh, new links. You only need to upload your PGP key or let the platform create one. Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook.
First, Install A Reliable VPN
Many people (mostly criminals) use these sites to perform illegal transactions such as selling banned goods and services. The Dark Web—a hidden part of the internet accessible only through specialized software like Tor—has become increasingly significant as we enter 2025. Often portrayed as the internet’s shadowy underbelly, the Dark Web hosts marketplaces offering everything from privacy tools and digital currencies to more questionable, or outright illegal, products and services.
Advanced monitoring services like CyberNod offer businesses a critical defense, alerting them to potential leaks and helping protect their assets. By keeping a vigilant eye on dark web activity, CyberNod provides early warnings of compromised data, empowering businesses to take proactive measures to secure their information. The Deep Web includes all content not indexed by search engines.This isn’t necessarily illegal—it’s just private or restricted. Other dark web search engines worth investigating are Ahmia, Torch, NotEvil, and the Onion URL Directory—just type out some keywords for what you’re looking for.
Why Is It Critical To Monitor Dark Web Marketplaces?
If you know how to use Microsoft Word, you’re typically working with large files that span multiple pages. So, you’ll be happy to know there are several easy ways to delete a page in Word, including both blank pages and those you simply no longer need. To use the dark web safely, use as many privacy-enhancing tools or programs as you can, and do not identify yourself in any way to anyone for any reason. While visiting any of the sites you find on those Wiki sites, do not maximize your browser, as it can help identify you by your monitor resolution. Data, whether in the form of simple user credentials and passwords or proprietary trade secrets, can fetch quite a price on the dark web. The dark web might not interest you, but its denizens might have already cast their eyes on you, so approaching all of your business processes from a security-by-design perspective is essential.
The Australian Federal Police (AFP) participated in a Europol-led investigation that in 2024 shut down LockBit’s primary platform along with 34 servers across the US, the UK, Europe, and Australia. When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails. The major advantage of using a live OS such as Tails is that, on shut down, the OS wipes itself from the thumb drive you’ve installed it.

Is There A Future For Dark Web Marketplaces?
As terrible as its reputation may be, some vendors sell legitimate goods or services. Some customers even use the dark web to make anonymous purchases, especially in areas where privacy is a huge concern. Exodus Marketplace started to become popular after the shutdown of Genesis Market, and it replaced it successfully.
Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web. Quality and validity of the data it provides justify its higher cost over other marketplaces. The platform’s popularity continues to grow, attracting both new and returning customers. Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem. Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025.
Lifehacker has been a go-to source of tech help and life advice since 2005. Our mission is to offer reliable tech help and credible, practical, science-based life advice to help you live better. The dark web, for the uninitiated among you, is a virtual neighborhood beyond the borders of the normal, everyday internet (which includes the website you’re looking at right now). It’s somewhere Google and Bing don’t index, and you need special tools to get to it. Upgrade your lifestyleDigital Trends helps readers keep tabs on the fast-paced world of tech with all the latest news, fun product reviews, insightful editorials, and one-of-a-kind sneak peeks. Microsoft Word is one of the best word processors around, allowing you to craft powerful documents with an intuitive interface.
It has a bidding feature, with new batches of stolen data being frequently added. The second category consists of data stores, which specialize in stolen information. In 2023, the dark web attracted an average of 2.7 million daily users, with Germany now leading as the country with the highest number of Tor users, surpassing the United States for the first time in years. He recommends verifying market employees carefully, and to weed out law enforcement infiltration through barium meal tests. All of that means Telegram’s takedowns are by no means the end of the crypto-scam industry, says Robinson.
Leverage Free Cybersecurity Resources

OBMs serves as digital innovation hubs for criminal communities and can be used to discover new schemas of illegal activities. Digital infrastructure, also called information infrastructure or cyberinfrastructure, is a term which encompasses a socio-technical interconnected structure of systems, people and organizations (Henfridsson & Bygstad, 2013). In an era defined by digital connectivity, protecting sensitive, critical and personal information from cyber threats – including those originating from the dark web – is a strategic imperative. International Standards offer organizations a robust, globally recognized framework to strengthen cybersecurity resilience, mitigate risks and safeguard sensitive and critical data from unauthorized access and misuse. Some hackers offer ransomware as a service (RaaS), where cybercriminals can “rent” a strain of ransomware from its creator in exchange for a fee or a percentage of their ransom payments.



