If the specified user exists, force this user to change the password on the next login. Create a new user and set the password using the auth provider syntax. Remove all databases from the specified server, adding them to other servers as needed. The specified server is not allowed to host any new databases.
About Cypher Market
The isEmpty() function returns true if the given LIST or MAP contains no elements, or if the given STRING contains no characters. The collect() function returns a single aggregated list containing the non-null values returned by an expression. Property values of nodes and relationships can be accessed statically by specifying a property name after the .
Elevate Your Cypher Market Shopping With Our Top-Tier Aggregator
Subsequently, users can narrow down their search by selecting product type, shipping locations, and price range. All that has been said above about node uniqueness constraints also applies to relationship uniqueness constraints.However, for relationship uniqueness constraints there are some additional things to consider. Because the Person node named Keanu Reeves already exists, this query does not create a new node.Instead, it adds a timestamp on the lastSeen property.
Given property uniqueness constraint on the name property for all Person nodes, the below query will match the pre-existing Person node with the name property Oliver Stone. Cypher prevents getting conflicting results from MERGE when using patterns that involve property uniqueness constraints.In this case, there must be at most one node that matches that pattern. Grant SHOW TRANSACTION privilege to list transactions by the specified users on home database to the specified roles. Grant SHOW TRANSACTION privilege to list transactions on all users on all databases to the specified role. Deny CREATE NEW TYPE privilege to create new relationship types on all databases to the specified role. Set the default Cypher version for a remote database alias when creating it.
XLM Declines 8% As Institutional Investors Retreat Amid Market Uncertainty
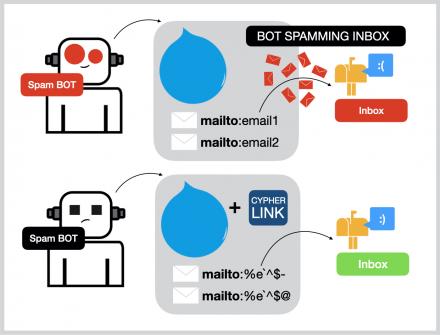
We’re not just a platform – we’re a community of passionate cypher url enthusiasts and cypher darknet market connoisseurs who are committed to pushing the boundaries of what’s possible. Through strategic partnerships, cutting-edge technology, and a deep understanding of customer needs, we’re laying the foundation for a new era of cypher website shopping. Imagine a world where discovery, personalization, and unparalleled convenience are the norm, and where your every cypher url and cypher darknet market desire is effortlessly fulfilled.
Scalar Functions

Grant SET PROPERTY privilege on a specified property, on all relationships with a specified type in a specified graph, to the specified role. Revoke MATCH privilege on all graphs and all nodes with either foo_label or bar_label and with a secret property that is null from the specified role. Grant READ privilege on all graphs and all nodes with a secret property set to false to the specified role. Deny READ privilege on a specified property, on all relationships with a specified type in a specified graph, to the specified role. List the currently logged-in user, returns only the default outputs (user, roles, passwordChangeRequired, suspended, and home). Modify a standard database named topology-example in a cluster environment to use 1 primary servers and 0 secondary servers, and to only accept read queries.
String Concatenation Operators
This may be due to some mathematical problem in our methodof private key calculation. Both decryptor functions rarely raise exceptions or result in an incorrectmessage. One of the reasons for that was, generated private key could be 1sometimes. The only remaining reason known for this issue is theinformation loss during multiplications of large numbers. Frequency of thisissue happening is measured to be around %4 with pypy3 as compiler. Only difference is that, this works by groupingcharacters by 2, appending their ascii values, using the resultant integer.With this method, this function is not an overcomplicated caesar cipheranymore.
Smart Online Booking
- Set the vector properties of a relationship using db.create.setRelationshipVectorProperty.
- List all available functions, returns only the default outputs (name, category, and description).
- Create a local alias named database-alias for the database named database-name.
- The date.statement() function returns the current DATE instant using the statement clock.
- Experience the ultimate in convenience, quality, and customer satisfaction as you explore the vast array of cypher url and cypher darknet link our aggregator has to offer.
- With respect to Drupal, encryption/decryption of field values happens over ‘Cypher Link’ field-formatter.
As Charlie Sheen and Oliver Stone do not know each other in the example graph, this MERGE query will create a KNOWS relationship between them.The direction of the created relationship is left to right. As of Neo4j 5.20, specifying a property of an entity (node or relationship) by referring to the property of another entity in the same MERGE clause is deprecated. DCode therefore proposes, on this page above, an artificial intelligence tool dedicated to the automatic recognition/identification of encryption and direct links to dCode tools capable of deciphering the message/text. To decrypt / decipher an encoded message, it is necessary to know the encryption used (or the encoding method, or the implemented cryptographic principle).
Query the relationship vector index review-embeddings for a neighborhood of 10 similar reviews to the vector given by the query parameter. Drop the index named index_name, throws an error if the index does not exist. List all indexes and return only specific columns using the RETURN clause.Note that YIELD is mandatory if RETURN is used. The create syntax is CREATE VECTORTEXTPOINTFULLTEXTLOOKUPRANGE INDEX …. The date.truncate() function truncates the given temporal value to a DATE instant using the specified unit. The toString() function converts an INTEGER, FLOAT, BOOLEAN, STRING, POINT, DURATION, DATE, ZONED TIME, LOCAL TIME, LOCAL DATETIME or ZONED DATETIME value to a STRING.
Our summer camp treasure hunts got so much more exciting with this tool! I create encoded clues that kids have to decode, and they absolutely love it. The Caesar shift option is particularly great for beginners, and it’s helping kids develop problem-solving skills while having fun. Generate classic shifted-alphabet codes by moving letters a set number of positions in the alphabet.

Cypher Marketplace
CALL subqueries can be used to further process the results of a UNION query.This example finds the youngest and the oldest Player in the graph. Optionally CALL a subquery.Similar to OPTIONAL MATCH, any empty rows produced by the OPTIONAL CALL will return null and not affect the remainder of the subquery evaluation. A CALL subquery is executed once for each row.In this example, the CALL subquery executes three times. List all procedures that can be executed by the current user and return only the name of the procedures.
1 Password Cracking Techniques

Based on in the CYPHER Stent PostMarket Registry in 2003 and the e-SELECT post-market. Grant all privileges to manage composite databases to the specified role. Grant SET DATABASE ACCESS privilege to set database access mode for standard databases to the specified role. Grant CREATE DATABASE privilege to create standard databases to the specified role.
- Grant SHOW TRANSACTION privilege to list transactions by the specified users on home database to the specified roles.
- Grant INDEX MANAGEMENT privilege to create, drop, and list indexes for all database to the specified role.
- The website is only functional on computers and other devices with large screens, and the interface lacks any responsive design elements.
- By mastering these challenges, you enhance your understanding of encryption techniques and their real-world applications.
- It returns the same as SHORTEST 1, but by using the ANY keyword the intent of the query is clearer.
Aggregating Functions
With password hashes from the database or encrypted SSH keys, cracking is necessary. To kickstart your reconnaissance in Cypher, begin by scanning the target using tools like Nmap or Masscan to identify open TCP ports and services, including SSH and potentially using a bash script for further automation. Utilize gobuster for directory enumeration, scour disclosed information for potential vulnerabilities, and execute basic scans for a deeper understanding of the system. Prioritize identifying any entry points like login pages or exposed APIs, which may require a password. Run services on standard TCP ports such as HTTP (80) and HTTPS (443) to unveil any weaknesses. Remember, thorough reconnaissance lays a solid foundation for successful exploitation.