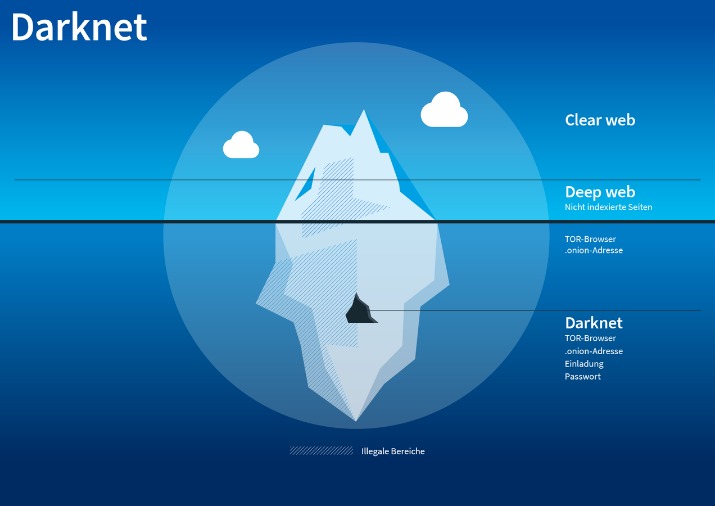
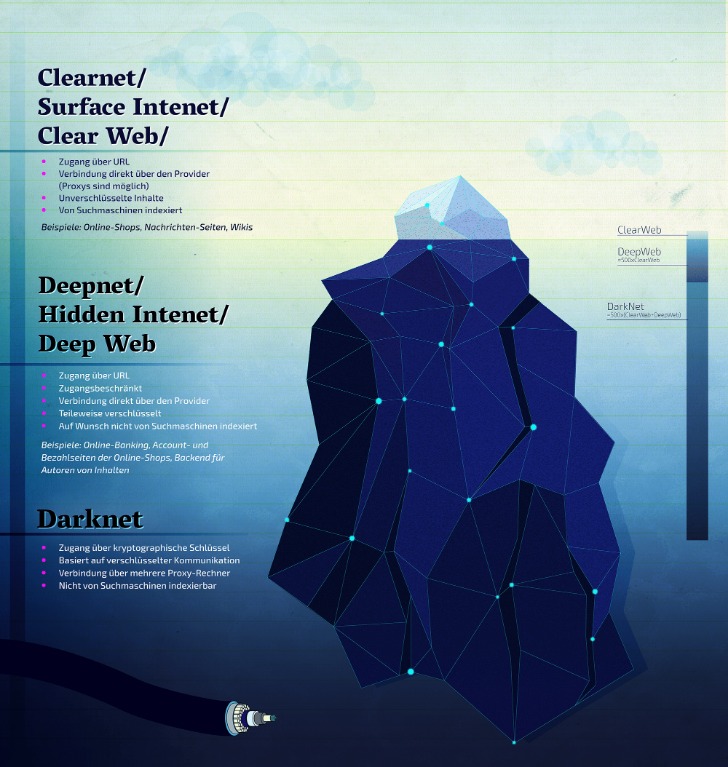
The Darknet is often utilized for secure communication, discreet information or file sharing, anonymous research without identity exposure, and occasionally for engaging in illicit activities. It is also recognized for hosting underground black markets(darknet markets), whistleblowing platforms, and discussion boards that champion freedom of speech. Non-crypto-native money laundering involves off-chain criminal activities, such as narcotics trafficking and fraud.
However, the evolution of the S2S network shows a different pattern than that observed in both the multiseller and the multibuyer networks. It’s essential to use a VPN, like Forest VPN, to secure your data, avoid clicking on unfamiliar links, and never disclose personal information. Additionally, using antivirus software and strong passwords can further protect you from potential threats.

The Top 10 Darknet Marketplaces Of 2025
These actions reflect broad collaboration involving Europol, the Dutch Police, the U.S. In Southeast Asia, the general public have mainly heard about the Darkweb on the news and through social media. It is assessed that only a minority have used it personally (see “Darknet Use in Southeast Asia” in Appendices).
As always, we must caution that these figures are lower-bound estimates, especially so for off-chain crimes, as many scams and fraud go unreported. The Chainalysis Crypto Investigations graph below demonstrates this type of behavior in a known scam group targeting the elderly. In this scenario, the scammer likely instructed their victims to use a specific service, Exchange 1, to purchase crypto assets. Each victim was then directed to send funds to a different wallet controlled by the scammer. The scammer subsequently consolidated these funds into a single wallet before cashing out at Exchange 2. Transactions in excess of these values trigger additional scrutiny, while transactions under these thresholds, even by just a dollar, do not face the same level of inspection.
Law Enforcement Involvement & Seizures
- Bank Secrecy Act (BSA) requires reporting on cash transactions exceeding $10,000.
- This material is not intended to provide legal, tax, financial, investment, regulatory or other professional advice, nor is it to be relied upon as a professional opinion.
- However, you must wait some time to reassess this marketplace because it’s been shut down.
- Once you unknowingly install the spyware or ransomware, they can steal your identity or even hijack your crypto wallet.
- The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures.
Download Tor Browser from torproject.org—your entry to the onion network. Some countries have just one or a few vendors with a loyal customer base and a wider selection of goods. For example, in India, one of the most frequent listings is for generic medication, which mostly comes from the first vendor shown below.
Nevada “Network Security Incident” Shuts Down State Offices And Services
The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures. In 2013, the FBI shut down the Silk Road, but it was later relaunched in 2014 with the new name of Silk Road 2.0, but the German authorities shut it down in the same year. Other than the Silk Road 2.0, similar marketplaces also emerged, but they all went down sooner or later.
THERE IS A PAUCITY OF RELIABLE DATA REGARDING DARKNET-ENABLED CRIME IN SOUTHEAST ASIA
Others are looking for stolen data, hacking services, or even banned books and political content. For sellers, it’s often about making money while staying off the radar. Cryptocurrencies and related laundering services are evolving as criminals seek to move towards more privacy-preserving currencies. Bitcoin remains the primary tool to exchange crypto to fiat (currency issued by a country). States are encouraged to engage with UNODC, the Financial Action Task Force (FATF) and industry to counter the threat posed by virtual-asset-based illicit financial flows and money laundering.
Use Cryptocurrency For Transactions
The site gives out free samples of the stolen data every now and then to gain more customers. With its fast rise to fame and focus on money fraud, it’s no surprise that cybersecurity experts are keeping a very close eye on this one. Exodus Marketplace started to become popular after the shutdown of Genesis Market, and it replaced it successfully.
Why Brand Monitoring And Threat Intelligence Are Stronger Together: 15 Key Benefits
It’s not as community-driven as Bohemia, but the polish makes up for it—feels like a pro operation, not a fly-by-night deal. If you’re after a darknet market with variety and a forward-thinking edge, Tor2door Market’s a contender—watch it close in 2025 as that AI kicks in. Bohemia popped up post-Hydra takedown and brings a fresh vibe—drugs (weed, pills, some coke) and digital goodies like hacked logins, no exact listing count, but it’s growing fast. They take BTC and Monero, and the site’s got a sharp, modern look—vendor profiles are loaded with ratings and reviews, easy to skim. What’s dope is their forums—real talk, not just noise—building trust like Telegram’s side hustle vibe.
The chart below shows this counterparty decline, as well as a drop in crypto flows across the fraud shop ecosystem. When looking at crypto inflows to DNMs in 2024, the data indicate that wholesale drug purchases were dominant, averaging between 71 and 81% of this year’s total market share. For online pharmacies, wholesale purchases led in 2024, followed by large retail.

On June 1, 2011, a Gawker report introduced the Silk Road marketplace to the public. That attracted the attention of politicians like US Senator Chuck Schumer, and federal agents were put on the case. The Silk Road website worked through Tor, which masks user identities by routing encrypted requests through a series of nodes.
Some chase banned goods—like a coder I met hunting censored PDFs—others love the mask it offers. The darknet kicked off with Tor back in the early 2000s, cooked up by the U.S. Then came Silk Road in 2011—imagine a guy in his basement flipping the switch on what folks called “the eBay of drugs.” It sold everything from weed to fake IDs until the FBI nabbed Ross Ulbricht in 2013.
Nevertheless, by analysing the income of each multiseller, we observe that the median income still reflects their high income, as shown in Fig. Individually, they are able to yield significant high incomes compared to other types of sellers. Throughout the whole period of observation, the dominant category of buyers is market-U2U buyers followed by market-only buyers, representing on average 52% and 42% of all buyers, respectively.
Market Operations
You can access it for legitimate purposes like whistleblowing and freedom of expression. However, it’s also used for illegal activities like drug trafficking, weapon sales, and stolen data trading. Law enforcement agencies monitor it for criminal activities, but legitimate users rely on it for privacy protection. In order to investigate the role of direct transactions between market participants, we now analyse the evolution of the S2S network, i.e., the network of the U2U transactions involving only sellers. Although the S2S network is composed only of U2U transactions, all categories of sellers (i.e, market-only, U2U-only, and market-U2U) are present in the S2S network.
In this post, we’ll walk you through the top 10 dark web marketplaces that you need to watch for potential threats to your organization. It’s all about drugs and digital goodies, with BTC and Monero on deck. Quality beats quantity here—their listings aren’t massive, but they’re solid. The site looks sharp, and vendor profiles are packed with ratings and reviews. They’ve got forums where people actually talk, which builds trust—kinda like the Telegram vibe.