Looking ahead to 2023, there are several darknet markets that are expected to dominate the scene. Freenet, AlphaBay Market, Vice City, asap Market, DarkFox Market, Tor Market, Tor2Door, Cypher Market, and Archetyp Market are all poised for success. These markets offer a variety of products and services, ranging from drugs and weapons to counterfeit goods and hacking tools. However, it’s important to note that using these markets comes with significant risks, as law enforcement agencies are actively monitoring them. Additionally, the diversity of products available on darknet markets is unparalleled.
Global Crackdowns Leave Crypto Criminals Few Options
For journalists, intelligence agents, and everyday citizens living in oppressive regimes, the dark web is a critical tool for supporting free speech and open access to news. Unfortunately, this same benefit is also useful for criminals, who routinely leverage the dark web to peddle illegal or stolen goods, obtain malware or other malicious tools, and coordinate their nefarious activities. As the digital asset industry continues to evolve, the Chainalysis report serves as a crucial reminder of the persistent threat posed by cybercriminal activities.
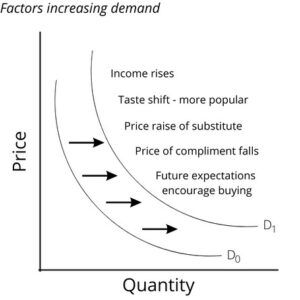
🧩 These statistics reveal the scale, anonymity, and sophistication of dark web operations—and why proactive dark web monitoring is no longer optional. However, you can trace its roots to the development of technologies like the Tor network or Freenet. In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet. This was the initial framework for anonymous communication and file sharing. Later in 2022, the US Naval Research Laboratory built on Freenet’s idea to create a secure and encrypted network for sensitive communications, which was later released to the public as open-source software. According to a recent trend, the dark marketplaces faced a decline in revenue.
Ransomware & Malware Ties To The Dark Web
Cross-check with PGP-signed mirrors on forums (e.g., Dread), and verify Abacus’s link via its official thread. ASAP’s USDT integration slashes costs by 20%, a trend growing 10% yearly—15% of ASAP trades in 2025. Stablecoins counter BTC’s volatility (30% price swings in 2024), appealing to 25% of traders seeking stability in crypto trading platforms. Torrez’s 200+ vendor boost in 2025 reflects a 20% growth trend across top 10 markets since 2024, totaling 11,000+ vendors.
Ethical And Legal Boundaries In Monitoring Darknet Marketplaces
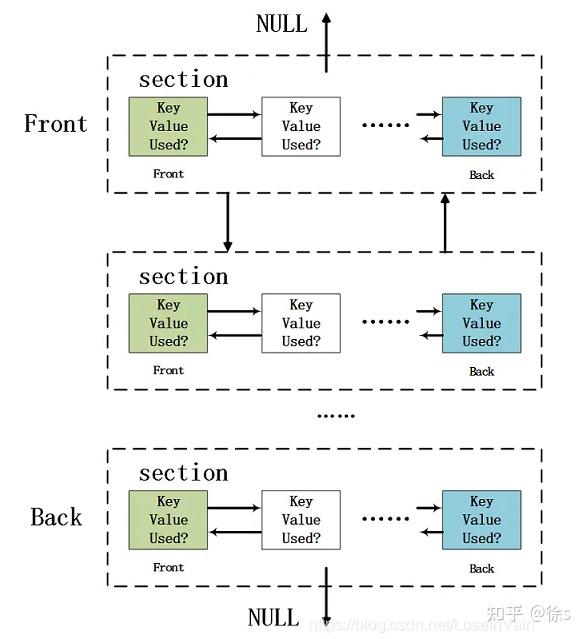
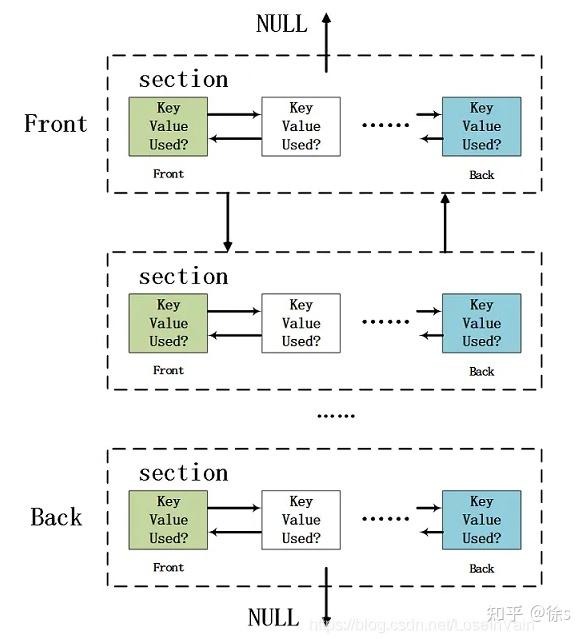
Dark-web marketplaces operate through encrypted networks, primarily utilizing anonymity-enhancing technologies such as Tor (The Onion Router) and I2P (Invisible Internet Project). These technologies obscure users’ identities and locations by routing their internet traffic through multiple volunteer-operated servers worldwide, making it extremely difficult to trace activities back to individuals. Tor remains the most prevalent method due to its ease of use and robust anonymity features, but the popularity of I2P is steadily growing due to its increased resistance to surveillance and censorship. The most traded data includes stolen credentials, credit card information, government IDs, malware kits, RDP access, fullz (complete identity profiles), and medical records. As cyberattacks and data breaches intensify in 2025, the volume of exposed credentials indexed on the dark web has reached unprecedented levels. It scans darknet marketplaces and hacker forums to alert you instantly if anything shows up.

Cyprus Airways Data Breach: Hackers Claim Access To Real-Time Systems And Passenger Records
In the face of increasing law enforcement activities, cyber criminals are increasing their security accordingly rather than exiting the cybercrime business. Drughub relies on AES-256 encryption without mandatory PGP, a simpler approach for its 8,000+ users. It lacks 2FA, a gap criticized post-2024 leak, but basic DDoS protection maintains 92% uptime. Its 93% escrow success rate resolves disputes in 48 hours for 80% of cases, solid but lagging behind top-tier security.
The dark web continues to act as the primary enabler of global ransomware and malware operations in 2025–26. From initial access brokers (IABs) to malware-as-a-service (MaaS) and negotiation platforms, nearly every stage of a ransomware attack has dark web fingerprints behind it. Sometimes, you might be hacked by using weak passwords or even just connecting to unsecured Wi-Fi on public networks.
AzureStrike – Offensive Toolkit For Attacking Azure Active Directory Environments
Transactions within these marketplaces typically leverage cryptocurrencies—most commonly Monero, Bitcoin, and privacy-centric digital currencies developed specifically to enhance transaction anonymity. Monero, in particular, has become the preferred cryptocurrency on the dark web in 2025 due to its advanced privacy mechanisms, which obscure transaction histories and wallet balances from public view. Silk Road quickly grew into the largest darknet market, handling hundreds of millions in transactions. But in 2013, law enforcement traced Bitcoin activity, monitored DPR’s forum posts, and exploited server vulnerabilities to identify Ross Ulbricht.
Role Of Law Enforcement Agencies (LEAs)
Besides this, it supports wallet-less transactions and accepts payments through Bitcoins, Litecoin, Monero, and Zcash. However, you must wait some time to reassess this marketplace because it’s been shut down. It issued a press release revealing that, from December 2021, the website won’t be functional anymore.

By signing up, you agree to the Terms of Use and Privacy Policy & to receive electronic communications from Vice Media Group, which may include marketing promotions, advertisements and sponsored content. This is a compilation of confirmed official Tor links to serve only as an anti-phishing resource. DarkNetMarkets have been keeping an eye on admin discussions, and some expected the ban hammer to fall for quite some time now. For example, threat actors may employ AI tools to gather information about individuals from social media and other online sources, crafting highly targeted attacks that are harder to detect. According to the FBI’s Internet Crime Complaint Center (IC3), losses from social engineering scams reached over $2.4 billion in 2022, and this figure is expected to rise as attackers refine their methods. CVV stands for “card verification value,” which is a unique code printed on payment cards that’s used to authorize payments made online or over the phone.

Our calculator below helps traders convert between BTC, XMR, and USDT, reflecting real-time preferences in the anonymous marketplace ecosystem. Navigating the darknet markets of 2025 requires more than just access—it demands strategy, caution, and knowledge to thrive in the anonymous marketplace ecosystem. This section offers an extensive set of pro-level trading tips for our top 10 darknet rankings, designed to help both novices and veterans maximize safety, efficiency, and success as of February 27, 2025. From securing your Tor setup and verifying onion links to leveraging escrow systems, encrypting communications, and choosing the right cryptocurrency, these tips cover the essentials of dark pool trading hubs. Whether you’re trading on Abacus, Alphabay, or Drughub, these insights ensure you stay ahead in the deep web markets.
- TRM Labs noted that darknet users tend to migrate to the next “reputable” option when a marketplace falls.
- The more proactive you are, the better you can protect yourself against identity theft and other cyber threats.
- Disputes occur in 3% of transactions, with 80% resolved within 48 hours, supported by a 93% escrow success rate.
- It scans darknet marketplaces and hacker forums to alert you instantly if anything shows up.
- These software are also capable of launching DDoS attacks and phishing campaigns.
This marketplace accepts payments via Monero but also supports the Escrow system. Using a reliable VPN provider helps keep you safe when you access marketplaces on the dark web. A VPN encrypts the data traffic and keeps your activities private on the dark web. It also masks your IP address, making it difficult for government agencies to monitor or track your activities.