It takes time to get the secure setup, which is described in the DNM bible, working. Once you finished the initial setup it will be pretty easy though. For future orders you just have to repeat the same steps for ordering on the secure setup that you already have. While not based in Australia, Abacus Market gained strong traction with local darknet users by embracing cultural references, supporting Australian vendors, and featuring a dedicated moderator from the region. These efforts helped it become one of the most active platforms among Australian users. Arresting vendors often has a greater disruptive impact than taking down DNMs.
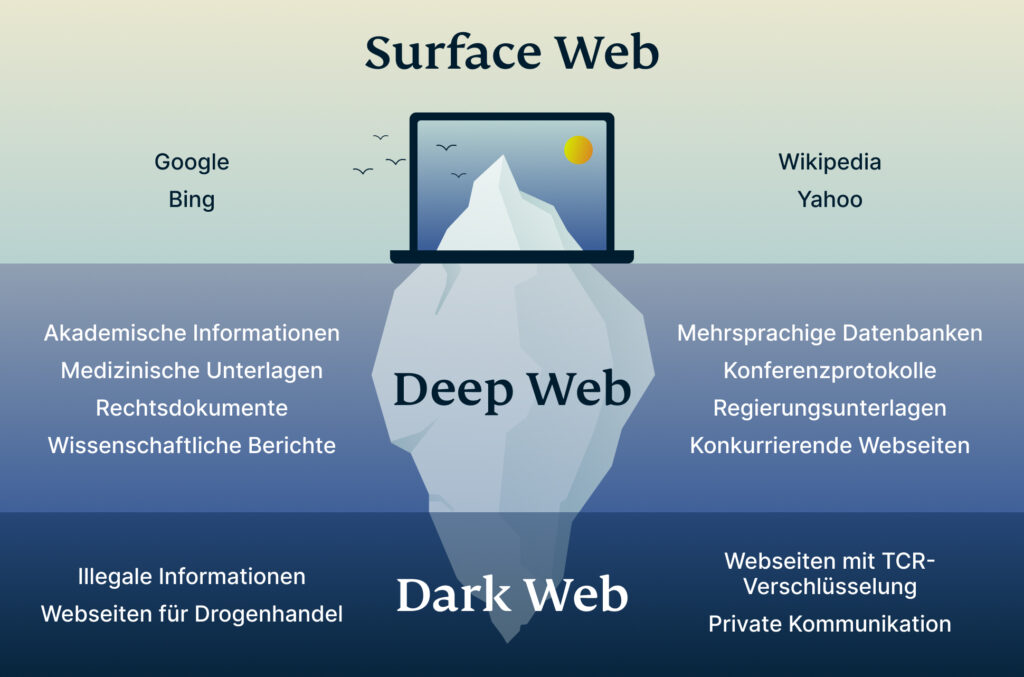
To get into DNMs, you’ll likely have to figure out the basics of things like PGP encrypted messages and using the TOR browser. TOR Browser is a free, modified version of the Firefox web browser configured to connect to the TOR network. You may also use it to access the regular internet more anonymously.
Blockchain
- However, the increased fees and slow transaction times are forcing darknet users to consider other coins.
- Established in 2020, Awazon Market has quickly become one of the most famous darknet marketplaces.
- Law enforcement agencies and cybersecurity experts must stay one step ahead, constantly adapting and evolving their strategies to counter the ever-changing tactics employed by malicious actors.
- It allows you to buy and sell a wide range of products and services with a good user experience.
Due to being the most popular and the oldest coin, Bitcoin is traceable. However, Monero, on the other hand, is untraceable and the most trusted payment method on these markets. Therefore, most cybersecurity experts recommend using Monero while shopping on darknet markets. Cybercriminals go on dark web marketplaces to buy and sell illicit goods and services. They engage in financial crime and sell other people’s stolen personal information, since they’re under the veil of anonymity.
Do I Need A VPN If I Use Tor?
There’s also a search bar that you can use to search for any particular product or vendor. Below are the best marketplaces on the dark net that we hand-picked after going through multiple shops and doing extensive research. For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy.
Run Antivirus/Anti-Malware Software
However, these were just the results of one forum on the darknet and hence cannot be considered as a comprehensive representation. After doing a more thorough analysis, the team concluded that Bitcoin was still the vendor coin of choice on the networks. The investigators at Recorded Future then went on to try and establish which of those coins are beginning to replace Bitcoin as the currency of choice on the Darknet. Actually, it’s better not to dive into the parallel world of the darknet whatsoever. Beyond the digital landscape, I seek solace in the open road, riding my cherished motorcycle and experiencing the exhilarating freedom it brings. These moments of liberation propel me to think differently, fostering innovative perspectives that permeate my work.
DragonForce Ransomware Hits Saudi Firm, 6TB Data Stolen

According to the research performed by analytical company “Recorded Future”, Monero is widely used in the Western world, while Russian “colleagues” prefer Litecoin. According to Australian studies, 47% of all bitcoin transactions happen on the darknet. This level of security is particularly appealing to those operating on the dark web, as it provides a level of protection for their illicit activities. However, this convergence has also presented significant challenges for law enforcement and regulators, as tracking and monitoring transactions on the dark web can be exceptionally difficult. But as I always try to challenge my ideas to make sure I’m on solid ground, I started digging deeper.
Microsoft Strengthens Security After China-Linked Attacks
These software are also capable of launching DDoS attacks and phishing campaigns. If for any reason, you decide to visit these hidden corners of the web, ensure you at least study and understand the common traps. Getting familiar with the tactics scammers use will go a long way in helping you protect your online data and assets. Some sellers offer cracked versions of expensive software that you’d typically pay hundreds of dollars for.
Why Addressing Legacy IT Is An Urgent Strategic Priority For CISOs
The reason is the same as why many regular Bitcoin users are abandoning the currency —the high transaction fees that take too much time to complete. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP. It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products.
As the DNM builds a small pool of users and sellers, it will snowball into a lucrative operation IF the service remains reliable and secure. Besides ever increasing hosting costs, the site will have to contend with authorities, attacks from hackers, and the occasional disgruntled market administrator. TorZon Market launched Sep 2022, supports XMR and BTC payments, has established vendors, and a user-friendly platform.

Their pseudonymous nature and decentralized structure offer a degree of privacy and security conducive to Darknet activities. Monero, a privacy-centric cryptocurrency, has gained significant popularity in the Darknet due to its advanced privacy features, including ring signatures and confidential transactions. It provides enhanced anonymity, making it a preferred choice for illicit transactions.
Overcoming The Challenges Of Decentralized Cryptocurrencies
All the payments were made through cryptocurrency, further enhancing marketplace anonymity. The users on this site can review and rate the products that promote reliable and fraudster vendors. In summary, the use of cryptocurrency, particularly Bitcoin and Monero, has revolutionized transactions on the dark web. The convenience, trust, and anonymity provided by these digital currencies have made them the preferred choice for illegal activities on hidden web platforms. However, it is essential to recognize that these illicit transactions represent only a fraction of the overall cryptocurrency market and should not overshadow the legitimate and innovative uses of digital currencies.
Accessing any darknet marketplace is dangerous because it is known to be a hub for illegal trade. In addition, several fake websites impersonate the famous dark net marketplace to obtain your financial and personal information and use it for malicious purposes. Monero, a privacy-focused cryptocurrency, has gained traction on the dark web due to its advanced privacy features. Unlike Bitcoin, Monero transactions are untraceable, making it a preferred choice for users seeking an extra layer of anonymity. The use of Monero has also been driven by its lower transaction fees compared to Bitcoin, making it more cost-effective for dark web transactions. In late June 2025, Abacus users reported withdrawal issues and decreasing trust in the platform.
Taylor says the cryptocurrency’s PrivateSend feature, which mixes up the origin and recipient addresses of transactions, accounts for less than 1% of overall transactions on the Dash network. “We believe that privacy is an important feature for users to have access to….but that has not equated to Dash adoption, let alone use, on the Darknet,” he said. One of the main challenges facing law enforcement is the decentralized nature of cryptocurrencies, which makes it difficult to track and monitor transactions. However, law enforcement agencies have been working to develop new tools and technologies to help them better understand and combat cryptocurrency use on the dark web. This has included partnerships with private sector companies and other government agencies to share information and resources.
This directory lists only established markets with verified onion links. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims. It is one of the most active and up to date markets and always provides new and updated malware and data. It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals. Using TAILS is yet another security measure that protects your online identity on the dark web. It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer.

It has a search option to let you find local and international products and services on the dark web. A lot of vendors from all over the world are registered here, offering an extensive range of products, including digital services, security tools, and other equipment. For those who are looking for a reliable Alphabay Market alternative, Awazon Market aspires to become the solution. To help maintain their anonymity, dark web black market users leverage a variety of tools and technologies that mask their identity and location. It’s important to know how these tools are used so you can perform reconnaissance and identify potential attacks or leaked information that can be used against you.